We’ve discussed how Censys has grown, and how Censys works as a platform. Today, we’ll talk about how we verify we have the best data possible. Dive deeper into the data in the original paper.
Comparing Censys to Ground Truth
Of course, when we are often the source of ground truth for various investigations, we need to find a way to measure how well our ground truth is covering the state of the world.
We first built our own “ground truth” by running random scans of 0.1% of the IPv4 space across every port using ZMap. Over one week we found 4.1 million services. We removed about 0.2% of hosts that behaved like fake “pseudo” services, or machines responding identically on dozens of ports, which can skew results despite being rare, and compared these independent scans to what we found in Censys.
We also evaluated Censys against Shodan, Fofa, ZoomEye, and Netlas. Since most of these platforms don’t let you export raw data or pull random samples, we used the following process:
- Generate 10K random IPs.
- Query Censys and the other tools for those IPs.
- Verify which reported services were actually online using ZGrab, which provides an independent comparison point to these scanning engines.
- Calculate how much real, current coverage each engine had.
Measuring Coverage and Accuracy
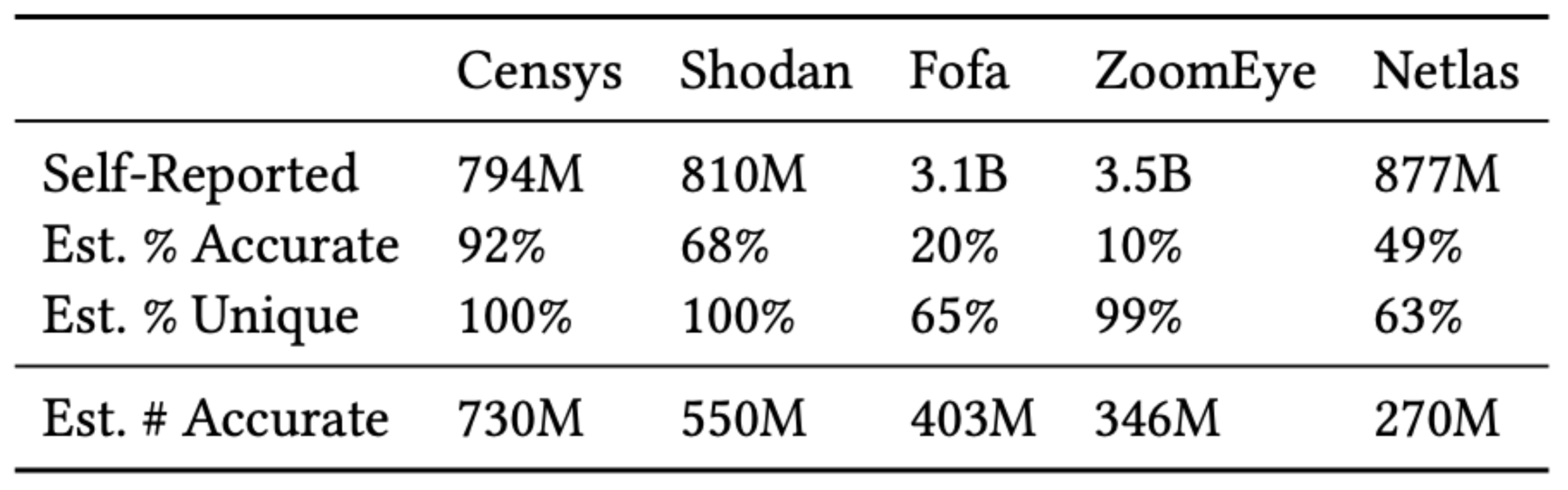
We started by comparing how much of the Internet each scan engine actually observes (coverage) and how accurate their data is compared to real-time follow-ups.
On paper, other tools claim to find more services than Censys, but in digging deeper we find that mostly reflects how they store or display data, not what’s really online.
After removing duplicates and outdated results, we see a different story: Censys has the highest coverage of active Internet services across the scanning engines.
This happens for two main reasons:
- Stale data: Many scanning engines do not prune out data. For example, only 10% of ZoomEye’s results were still online when we checked against our independent scan.
- Duplicates: Other scanning engines often double-count the same IP/port pairs, inflating their numbers.
While other platforms showed only 10–68% accuracy, Censys’ focus on pruning stale data pushes its accuracy to 92%.
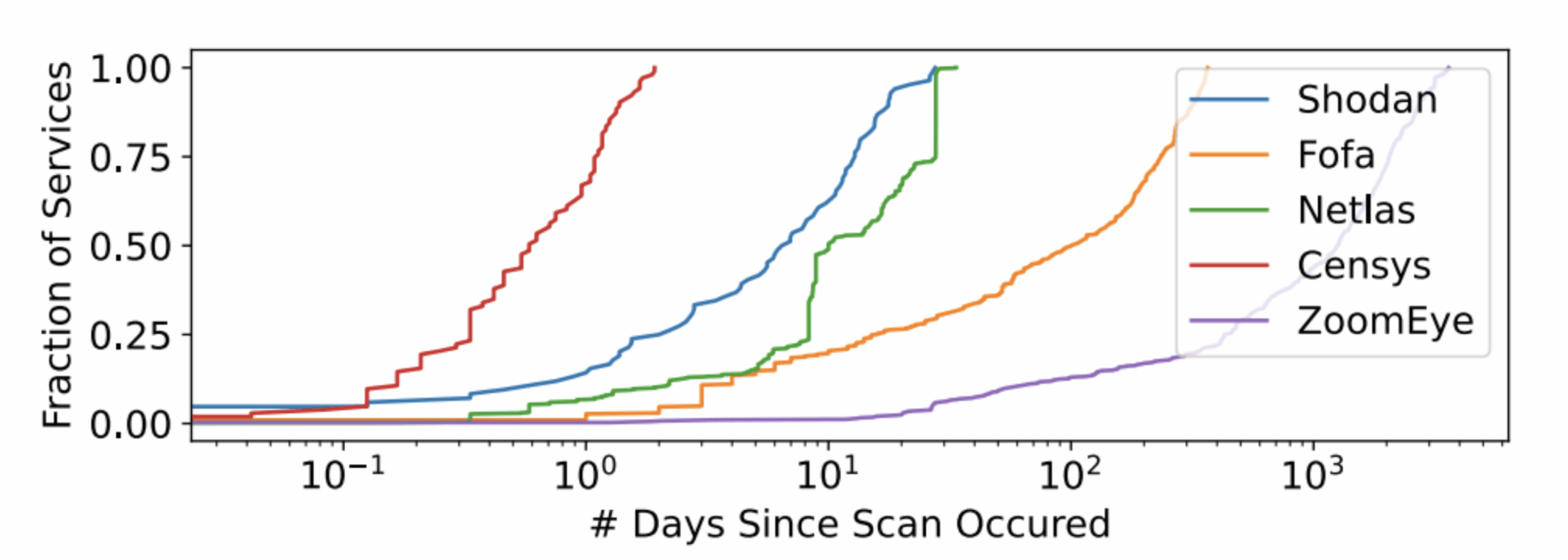
Data Freshness
To check how “fresh” each engine’s data really was, we looked at the last scanned date for every service that we interrogated. We found that while 100% of Censys’ results were scanned within the last 48 hours, this is not the case for other scanning engines, in some instances finding service entries that are over years old. Engines that scan more frequently also had more accurate results, which makes sense in the world of a fast-changing Internet.
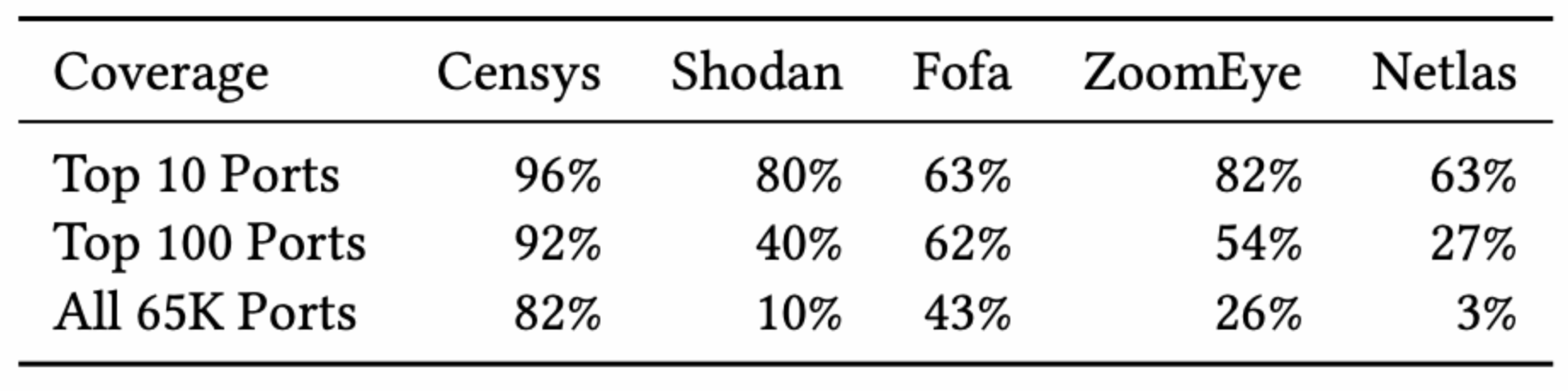
Port Coverage
Scanning busy ports is easy — scanning all 65K ports is what sets platforms apart. Censys performs well on both fronts, covering 96% of IPv4 services on the top 10 ports, 92% on the top 100 ports, and 82% across all 65K ports.
This broad coverage is a big reason for Censys’ visibility advantage. We follow the classic 80/20 rule: finding 80% of services is easy, and covering the last 20% takes extra work.
Coverage Overlap
We next check how much overlap each scanner has over the other. Each uses different scan schedules and methods, so there’s some expected gap.
When we compared overlap between engines, Censys captured 96% of Shodan’s active services, and 90% of Fofa and ZoomEye’s responsive services. Other tools only saw 39–57% of Censys’ results.
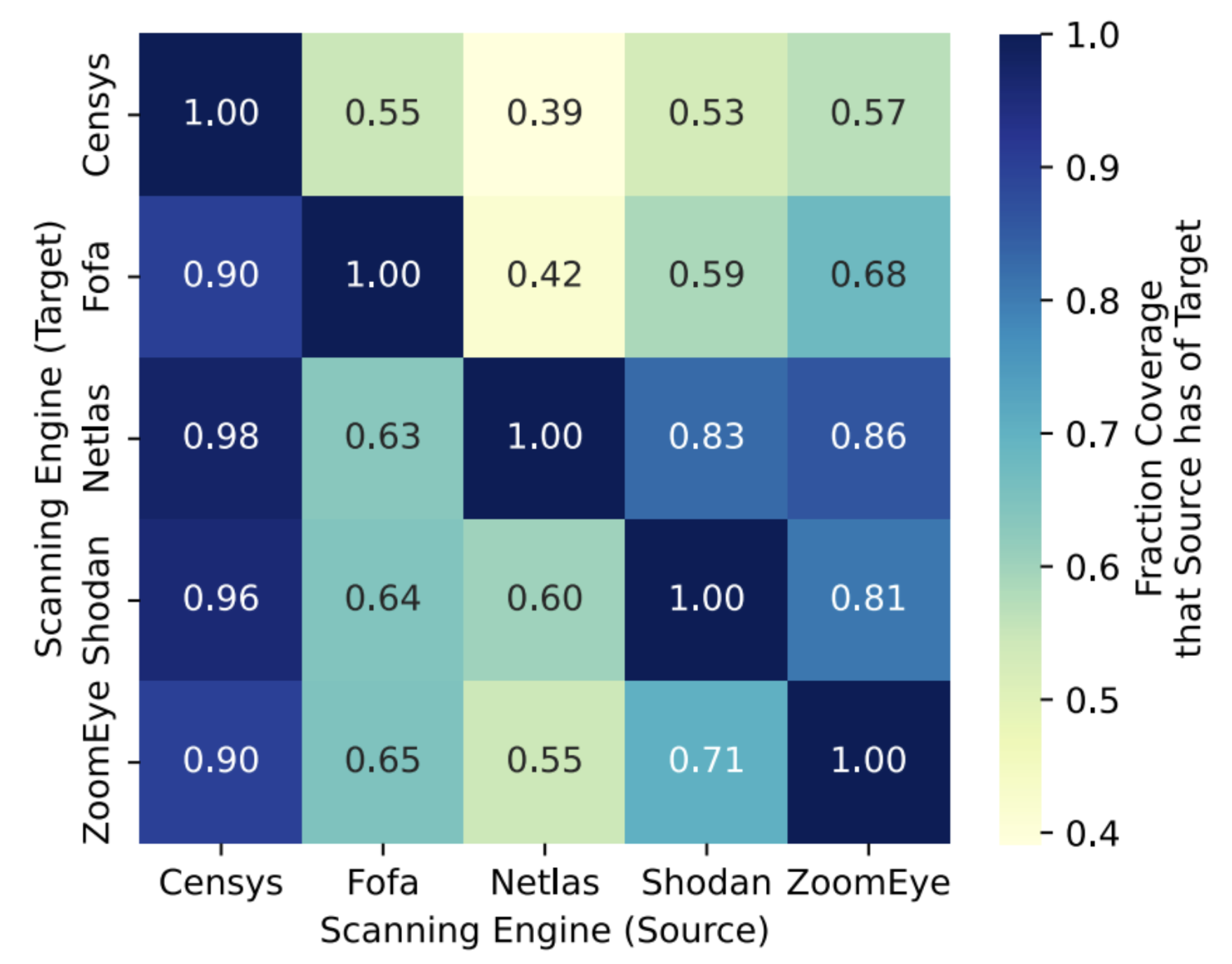
In short, Censys consistently covered more of what’s truly online, and with fresher, more reliable data.
Industrial Control Systems (ICS) Coverage
While Censys leads in overall Internet visibility, much of the web is made up of everyday HTTP(S) services — not all of which matter for security. To see how this visibility impacts a real security use case, we looked at Industrial Control Systems (ICS), the types of systems that run power grids, factories, and pipelines, and have been targeted in major attacks by Russia- and Iran-linked groups.
This experiment also let us test engines in a different way. In earlier sections, we couldn’t pull all data from every platform due to API and cost limits, so we used random samples. But with ICS, the total number of exposed systems is small enough that we can almost query them all across every scan engine. All tests ran in August 2024.
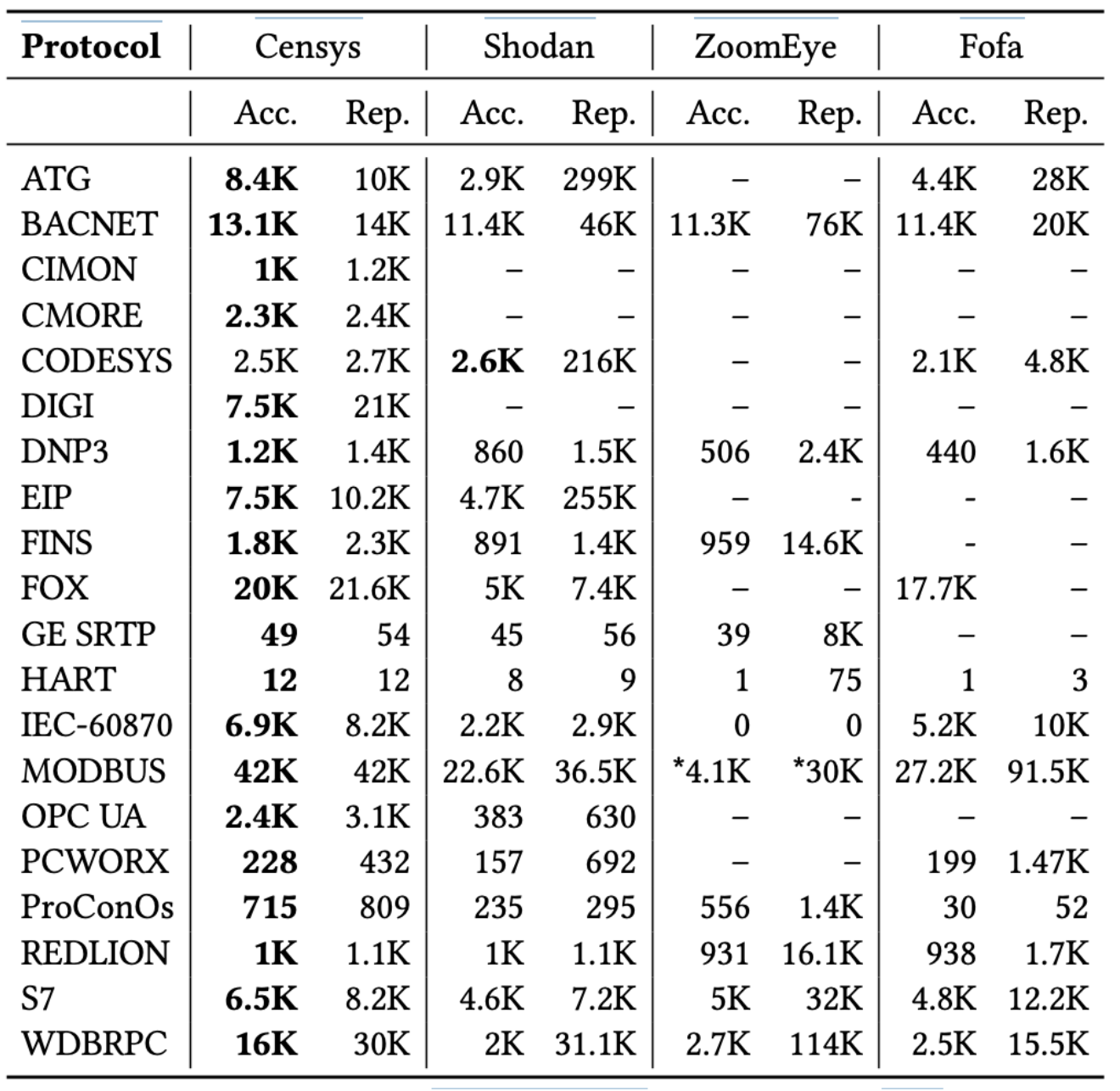
For most ICS protocols, we were able to pull complete data from every platform. The only exception was Modbus, where ZoomEye’s data was so stale that we stopped at 30K results, our remaining monthly download limit. Even with that, we covered all Modbus systems ZoomEye had scanned in the past 22 days.
As shown, Censys’ broader and fresher visibility translates directly into better ICS coverage for almost every protocol (except CODESYS). Part of that gap is due to many ICS devices using non-standard ports, but data freshness also plays a role — especially since many of these systems connect through LTE/5G networks, which frequently change IPs.
Numbers alone don’t tell the full story. Many platforms drastically overreport ICS systems because they rely on keyword matches instead of real protocol checks. For example, Shodan claims huge numbers of CODESYS devices just by flagging any service on port 2455 that includes words like “operating” or “system.” Upon checking, those are mostly plain HTTP servers, not real ICS devices.
Censys, by contrast, only labels a service as running a given protocol if it successfully completes a layer-7 handshake. This tighter verification dramatically reduces false positives and gives a far clearer picture of what’s actually exposed online.
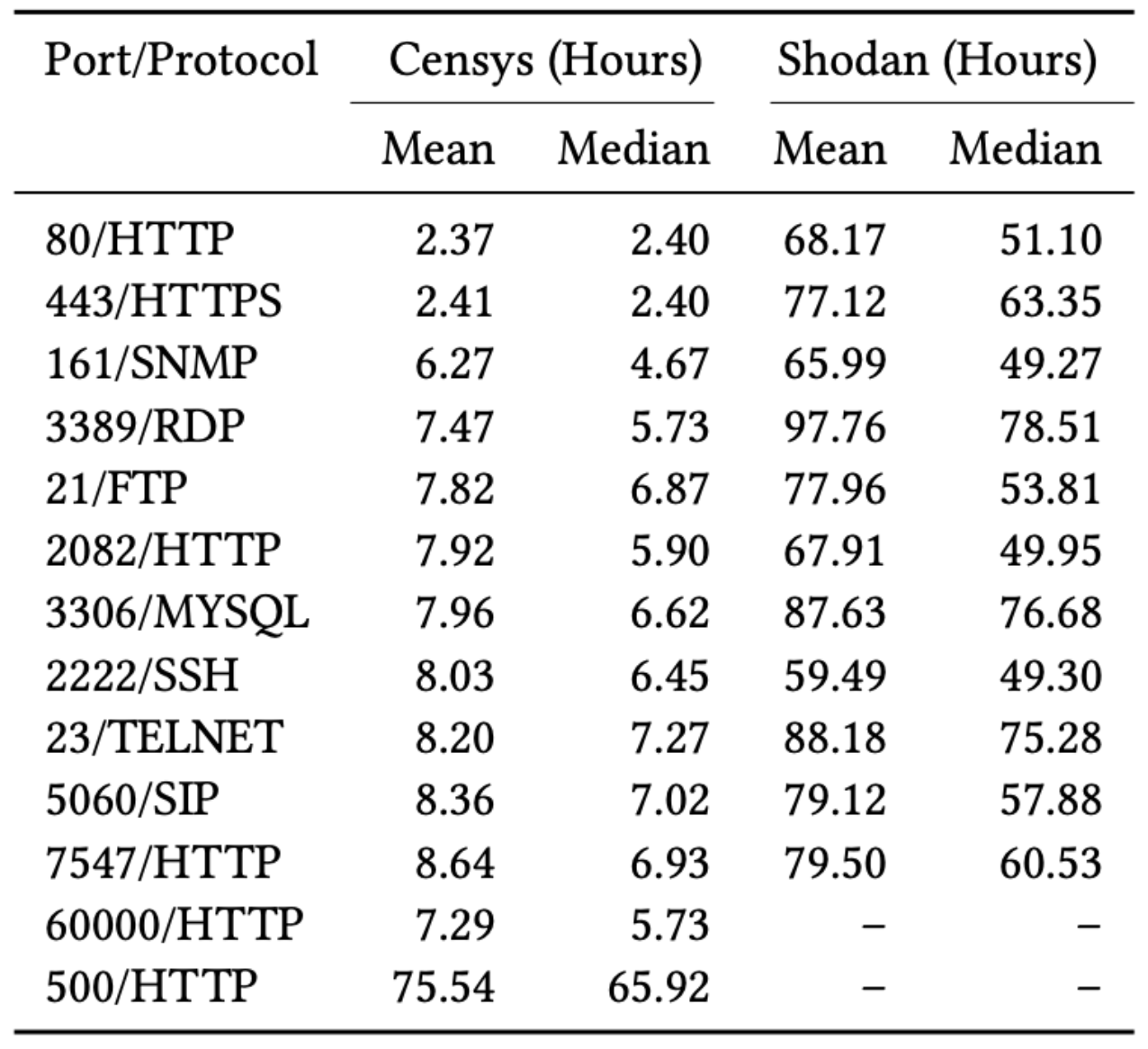
Time to Discovery
Censys isn’t just focused on finding all Internet services, it’s also designed to find them fast, right as they come online. To see how quickly it detects new hosts, we compared Censys and Shodan, the two platforms that clearly identify their own scanners. To test discovery speed, we needed to know exactly when a service first appeared online. So for a week we deployed 100 honeypots on Google Cloud, adding a few every eight hours to cover different scanning cycles.
Each honeypot used T-Pot’s Python honeypot framework and listened on 12 common ports. Then, we monitored how long it took before we saw connections from Censys or Shodan’s scanners.
Censys detected new services in about 12.3 hours on average (5.7 hours median), much faster than Shodan’s 76.5-hour average (60.9-hour median). Within just 24 hours, Censys found 100% of services for six of the most popular protocols, and within a week, it had detected everything across all tested protocols.
Conclusion
Overall, our findings show that Censys provides the most accurate, up-to-date, and comprehensive view of Internet-exposed services compared to other major scan engines. While competitors like Shodan, Fofa, ZoomEye, and Netlas often report larger totals, much of their data is outdated or duplicated, inflating coverage at the cost of reliability. Censys, by contrast, maintains fresher data, scans all 65K ports, and achieves 92% overall accuracy, offering stronger visibility across protocols, countries, and critical infrastructure systems such as ICS. Beyond accuracy, Censys also outperforms in speed, detecting new services hours to days faster than others. Together, these results highlight Censys as the most precise and responsive platform for understanding the live Internet and tracking how it changes in real time.
Come back next week for our final blog in the series, looking ahead to the future of Censys. In the meantime, experience the superior coverage, accuracy, and freshness of Censys data for free by creating a Free account.