
On February 2, 2026, Notepad++ published an update on the security incident they first disclosed in early December of 2025, confirming that their distribution infrastructure had been compromised between June and December 2025 and used to deliver a malicious installer to users downloading version 8.9.9.
Subsequent research by Rapid7 tied this compromise to a campaign attributed to the Chinese APT actor tracked as Lotus Blossom. According to R7’s analysis, the malicious installer was used as an initial access vector to deploy a custom backdoor dubbed Chrysalis, alongside commodity post-exploitation tooling such as Cobalt Strike.
While Rapid7’s work focused primarily on the malware functionality, the infrastructure associated with this campaign has continued to surface in internet scan data both before and after the public disclosure. In many cases, the infrastructure exhibits long-lived characteristics and reuses TLS certificates, enabling us to track it in our data over time.
This article examines network-level artifacts and pivots observable in Censys. Please understand that we’re not trying to enumerate all Chrysalis infrastructure; we’re only enumerating what is observable and pivotable via scan data.
Chrysalis Hosts
95[.]179.213.0 – GUP.exe Hosting
This host is associated with downloading a malicious GUP.exe, alternating among trusted VPN certificates, fake Cloudflare-looking certificates, and long-lived SSH services.
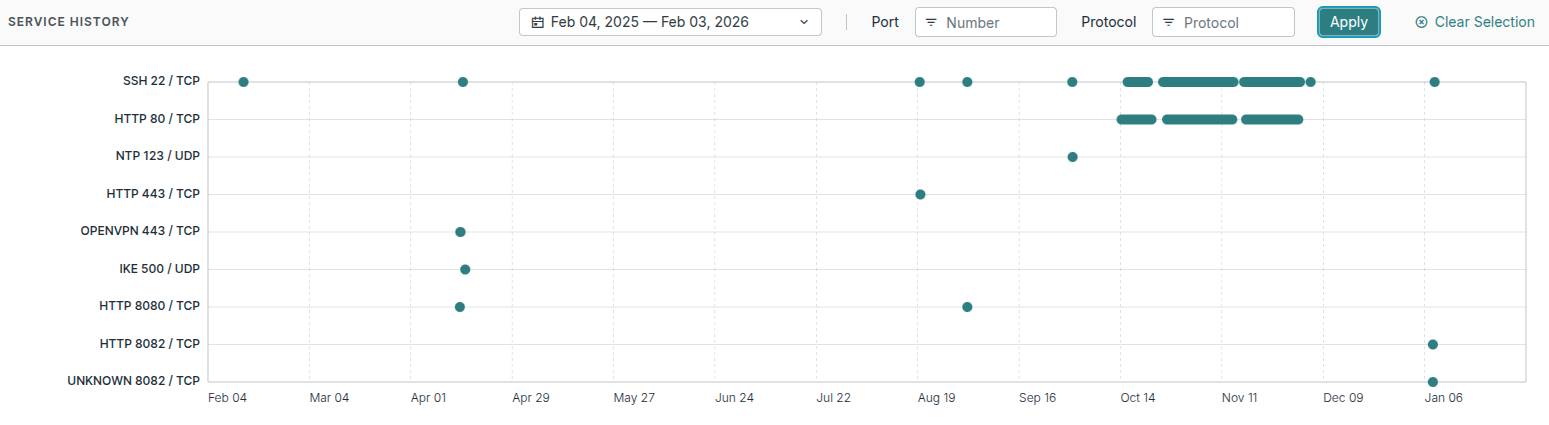
The first observed activity on this host occurs in mid-February 2025, when it exposes a single SSH service on port 22 (view @ 2025-02-12), which may indicate the host was first staged before any payloads were made available for download.
Two months later, in April 2025, the host significantly expanded its services. On April 13, it brought up an HTTP service on port 8080 and an OpenVPN service on port 443 (view @ 2025-04-13). The TLS certificate presented on port 8080 is issued for lazerpenguin[.]com, a domain associated with a commercial VPN provider used by McAfee called TunnelBear (certificate).
The following day, on April 14, the host briefly exposes an IKE service on UDP port 500 (view @ 2025-04-14). By April 16, all observed services disappear, and the host goes dark for several months.
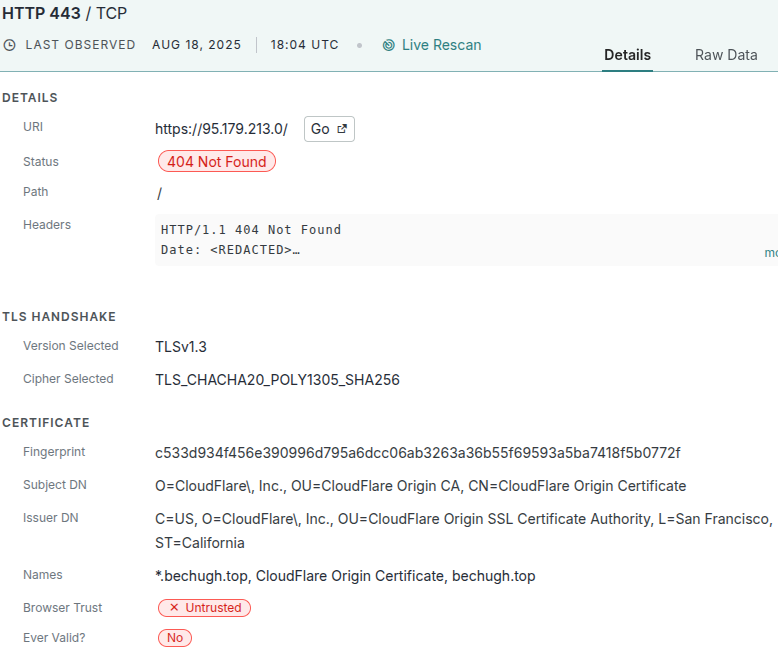
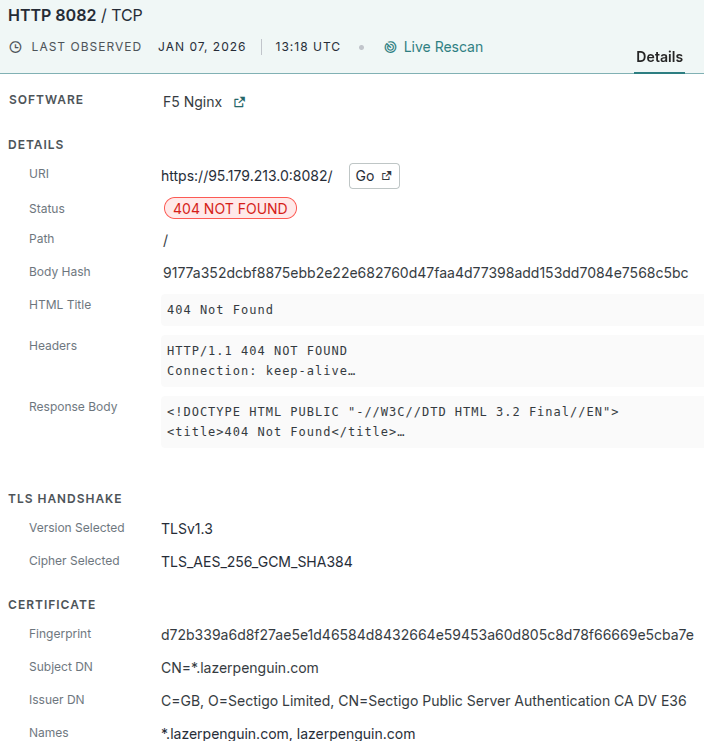
When the host reappears in August 2025, its external services appear to have changed significantly. On August 18, SSH returned to port 22 alongside an HTTPS service on port 443 (view @ 2025-08-18). This time, however, the TLS certificate is no longer tied to the TunnelBear VPN; instead, it resembles a Cloudflare-style origin certificate issued for the domain “bechugh[.]top” (certificate), a certificate that has since been observed across hundreds of seemingly unrelated hosts (search).
By August 20, both SSH and HTTPS services were taken offline (view @ 2025-08-20). Less than two weeks later, on August 31, the host returns once more with SSH on port 22 and HTTP on port 8080 (view @ 2025-08-31), again presenting a trusted lazerpenguin[.]com TunnelBear certificate. These two services disappear within a day.
Later, on September 29, 2025, the host exposes a new NTP server on port 123 and an SSH service on port 22 with a new host key (host key search), indicating that the underlying OS was likely reimaged or the key regenerated for a new owner.
This host continues this pattern into late 2025 and early 2026, alternating between SSH-only access, HTTP or HTTPS services on non-standard ports, and periods of inactivity. Its final observed configuration in early January 2026 shows SSH on port 22 and HTTPS on port 8082 (view @ 2026-01-08), using yet another lazerpenguin[.]com certificate (certificate).
It appears this host behaves more like a reusable staging asset than a single-purpose C2.
61[.]4.102.97 – Chrysalis C2 Endpoint
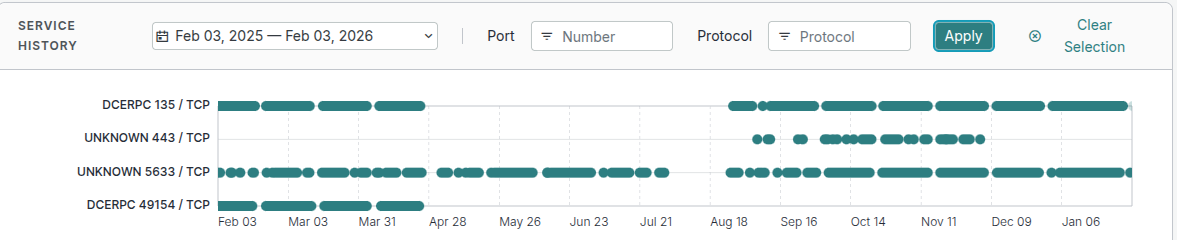
Rapid7 identified api[.]skycloudcenter[.]com as a Chrysalis command-and-control domain that resolves to IP 61[.]4.102.97 and exhibits a narrow operational footprint in Censys data as seen in our service history timeline:
The first observable activity in Censys occurs on September 4, 2025, when the host exposes a single unknown service on port 443 using a valid, trusted certificate issued to skycloudcenter[.]com (view on 2025-09-04). As we can see, Censys was unable to determine the service type during the service’s availability:
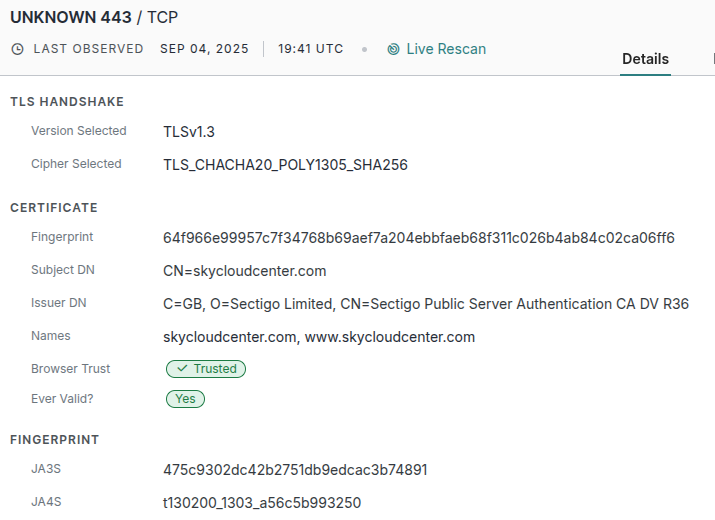
The certificate for this service (64f966e9) was also observed on another host (160[.]250.93.48) in early December, which we will cover in the next section.
On October 16th, 2025, the owner rotated out the TLS certificate on 61[.]4.102.97 (view on 2025-10-16), replacing it with a new certificate with the same issuer (certificate).
Unfortunately, this host appears to be well masked, with no clear indicators that it is a C2 server from a scanning perspective.
160[.]250.93.48 – Another host with the Chrysalis TLS certificate.
While this host was not listed in the original research by Rapid7, it was discovered due to the fact it was running the same TLS certificate as our prior host: 61[.]4.102.97.
On December 3, 2025, the host first appeared with an RDP service exposed on a non-standard port, 5633 (view on 2025-12-03). The following day, December 4, it exposes an HTTPS service on port 443, using the same 64f966e9 certificate as the Chrysalis C2 endpoint (view on 2025-12-04).
This TLS service is short-lived, disappearing by December 12; However, on December 23, 2025, the host exposes an SSH service on port 22 (view on 2025-12-23) which suggests the host was potentially transitioned to a different operator, and by January 22, 2026, both the SSH and RDP services are taken offline (view on 2026-01-22) and the host disappears from our view.
It should be noted that Censys is not claiming this to be another C2 server, but the fact that it runs the same TLS certificate as the verified C2 server on the same port hints at the same functionality
Chrysalis Variations
Rapid7 identified several loaders similar to Chrysalis malware but with different configurations. Here, we will look into the pivots that came from these samples to uncover the underlying infrastructure
Loader 1 – Stagers and Cobalt Strike
- SHA-256: 0a9b8df968df41920b6ff07785cbfebe8bda29e6b512c94a3b2a83d10014d2fd
- Shellcode SHA-256: 4c2ea8193f4a5db63b897a2d3ce127cc5d89687f380b97a1d91e0c8db542e4f8
- User Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/92.0.4472.114 Safari/537.36
- URL hosting CS beacon: https://59[.]110.7.32:8880/uffhxpSy
- CS http-get URL: https://59[.]110.7.32:8880/api/getBasicInfo/v1
- CS http-post URL: https://59[.]110.7.32:8880/api/Metadata/submit
59[.]110.7.32 & Certificate Pivots
The first loader described in the R7 blog was linked to the host 59[.]110.7.32, which evolves over time from hosting suspicious files to long-lived Cobalt Strike services.
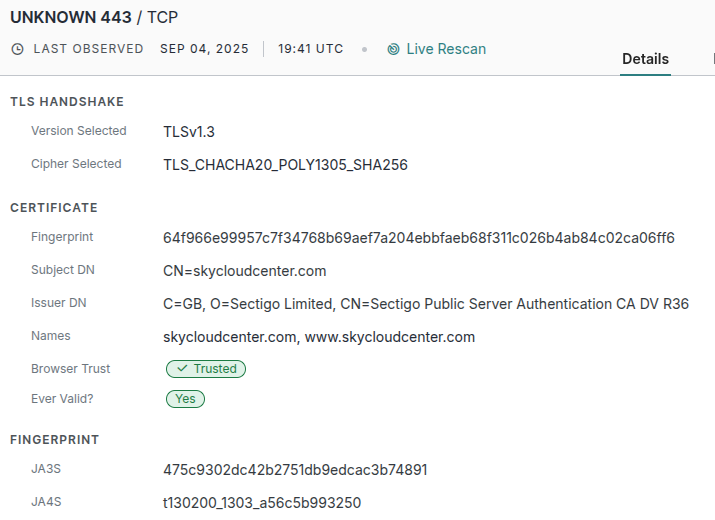
When this host first becomes visible in March 2025, its footprint is minimal: an SSH service on port 22 (view on 2025-03-14), followed shortly by an HTTP service on port 80 that exposes a Python-based open directory (view on 2025-03-18). The contents of this open directory included what appear to be small binaries, APKs, and some numerically named files, possibly containing a lightweight payload (screenshot below).
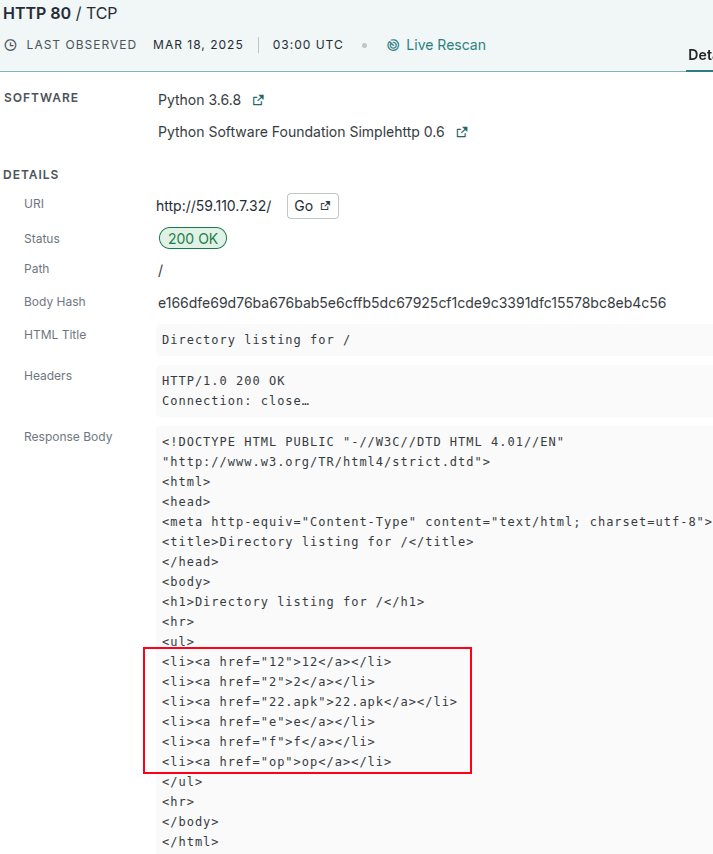
By early May, the role of this host shifts slightly. On May 7th, 2025, an unknown TLS service appears on port 17777 (view host), presenting a certificate that strongly resembles those generated by Cobalt Strike (view certificate) and described in a previous article on using Cobalt Strike to find more Cobalt Strike:
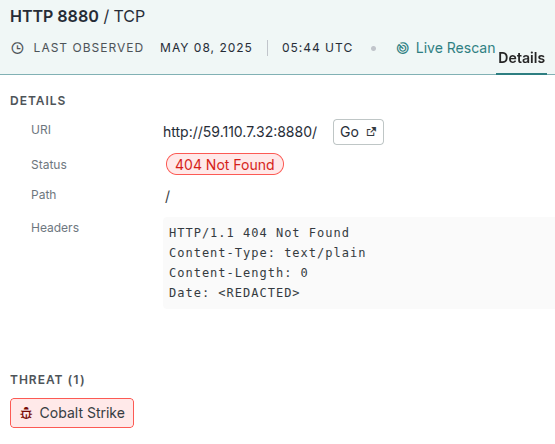
A day later, on May 8th, 2025, a Cobalt Strike server is found running on port 8880 (view on 2025-05-08). This is the port described in the Rapid7 research for this malware. While we were unable to pull down the beacon configuration from this host, it did match our Cobalt Strike fingerprint at the time:
Later that month, on May 22, 2025, the same host exposed another Cobalt Strike listener on port 80 (view on 2025-05-22). This time, however, we were able to fetch the beacon configuration!
Cobalt Strike Beacon (HTTP)
Target : 59.110.7.32:80
Sleep/Jitter : 60s / 0%
Kill Date : none
DNS / SSL : true / false
Cookie Beacon : enabled
Watermark : 426352781
SpawnTo (x86) : %windir%\syswow64\rundll32.exe
SpawnTo (x64) : %windir%\sysnative\rundll32.exe
HTTP GET x86 : GET /pixel (Cookie header)
UA : MSIE 9.0; Win7; Trident/5.0; NP07; NP07
HTTP GET x64 : GET /activity (Cookie header)
UA : MSIE 9.0; Win7; Trident/5.0
HTTP POST : POST /submit.php
Header : Content-Type: application/octet-stream
Param : idWhat’s interesting here is that the Cobalt Strike server on port 17777 shares the same TLS certificate (b9b62d) across three other hosts on different (overlapping) dates:
- On May 7, 2025, the host 47[.]120.61.164 (view @ 2025-05-07) was presenting the same TLS certificate observed on the unknown Cobalt Strike service at 59.110.7.32, while simultaneously running a separate Cobalt Strike listener with an active beacon on port 80, distinguished by a different watermark and distinct GET and POST paths.
Cobalt Strike Beacon (HTTP)
Target : 47.120.61.164:80
Sleep/Jitter : 60s / 0%
Kill Date : none
DNS / SSL : true / false
Cookie Beacon : enabled
Watermark : 987654321
SpawnTo (x86) : %windir%\syswow64\rundll32.exe
SpawnTo (x64) : %windir%\sysnative\rundll32.exe
HTTP GET x86 : GET /ga.js
UA : MSIE 7.0; Windows XP
Header : Cookie
HTTP GET x64 : GET /ptj
UA : MSIE 10.0; Windows 8; WOW64
Header : Cookie
HTTP POST : POST /submit.php
Header : Content-Type: application/octet-stream
Param : id- May 14, 2025 — the same Cobalt Strike–generated TLS certificate was observed on two additional hosts, 152[.]136.165.180 (view @ 2025-05-13) and 49[.]232.102.73 (view @ 2025-05-14). Both hosts exposed Cobalt Strike services; however, no retrievable beacon configuration was observed on either endpoint.
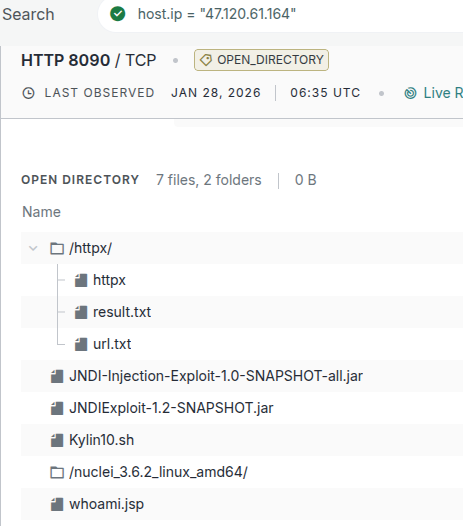
While all of these services eventually died off, just recently, on January 28, 2026, the host 47[.]120.61.164 was running an HTTP-based open directory on port 8090 (view @ 2026-01-28) containing files consistent with vulnerability scanning for JNDI-based exploits, including evidence of active reconnaissance against potentially vulnerable servers (httpx/results.txt) and a script named whoami.jsp, likely intended as a callback endpoint for exploitation attempts:
Loader 2
The second loader described by Rapid7:
- SHA-256: e7cd605568c38bd6e0aba31045e1633205d0598c607a855e2e1bca4cca1c6eda
- Shellcode SHA-256: 078a9e5c6c787e5532a7e728720cbafee9021bfec4a30e3c2be110748d7c43c5
- User Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/92.0.4472.114 Safari/537.36
- URL hosting CS beacon: https://124[.]222.137.114:9999/3yZR31VK
- CS http-get URL: https://124[.]222.137.114:9999/api/updateStatus/v1
- CS http-post URL: https://124[.]222.137.114:9999/api/Info/submit
124[.]222.137.114
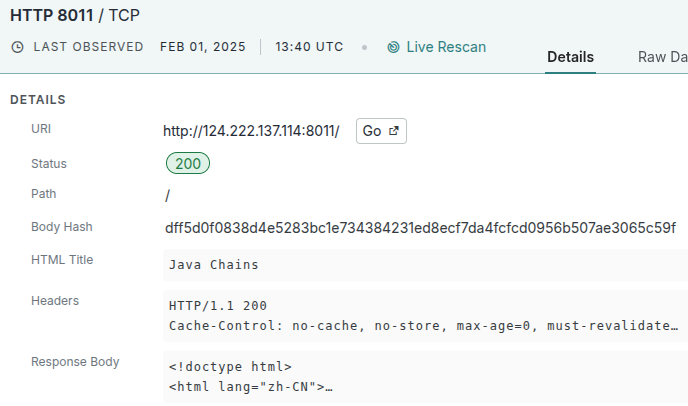
The second loader described by Rapid7 maps to a different infrastructure profile: the host 124[.]222.137.114 (view). The earliest observed activity on this host occurs in early February 2025, when it exposes a Java Chains (GitHub link) service, a Java-based exploitation application, on port 8011 (view):
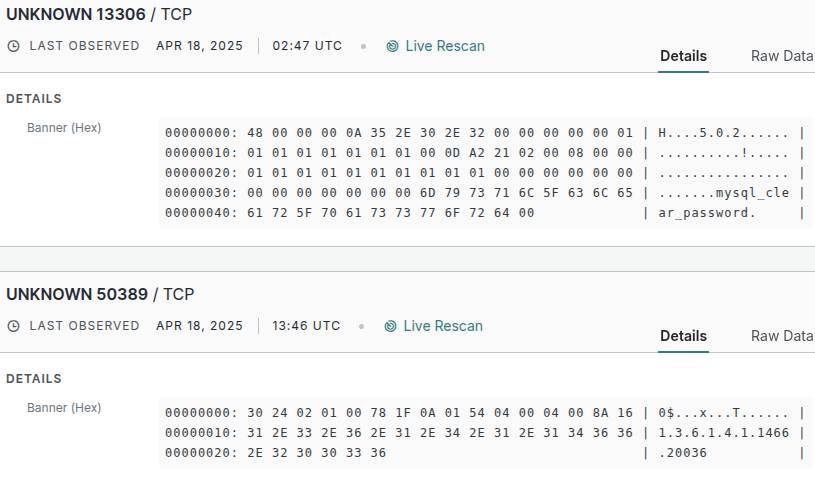
Over the following months, additional services appear: an SSH server on March 10, 2025 (view), a service consistent with MySQL on port 13306 on March 20 (view), and an LDAP service on port 50389 by April 18 (view). However, these two services were marked as UNKNOWN in Censys:
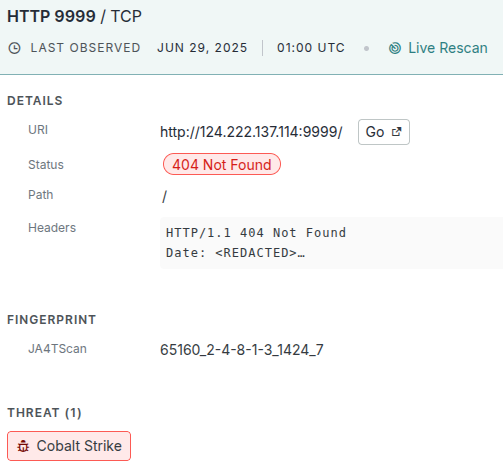
In June 2025, the host briefly exposed Cobalt Strike listeners on port 9999 (mentioned in Rapid7’s report) and later on port 23333, neither of which presented an observable beacon configuration (view on 2025-06-08; view on 2025-06-29):
By September 2025, the host loses most of its externally visible services and eventually goes fully dark (view @ 2025-09-24). When it reappears in October, it does so in an entirely different role, exposing Asset Reconnaissance Lighthouse (ARL) on port 15003 (view @ 2025-10-07):

The later appearance of ARL on this host likely indicates post-campaign infrastructure reuse or a transition to a different operator, but could still be in the same hands as the individual behind Chrysalis. This is malicious infrastructure transitioning into different types of malicious infrastructure.
Timeline
Early February 2025
- 124[.]222.137.114 exposes Java Chains, a Java-based exploitation application, on port 8011.
Mid-February 2025
- 95[.]179.213.0 exposes a single SSH service on port 22.
March 10, 2025
- 124[.]222.137.114 exposes an SSH service on port 22.
March 20, 2025
- 124[.]222.137.114 appears to expose a MySQL service on port 13306.
April 13, 2025
- 95[.]179.213.0 exposes an HTTP service on port 8080 and an OpenVPN service on port 443, presenting a TLS certificate issued for lazerpenguin[.]com.
April 14, 2025
- 95[.]179.213.0 briefly exposes an IKE service on UDP port 500.
April 16, 2025
- 95[.]179.213.0 loses all observed services and goes dark.s
April 18, 2025
- 124[.]222.137.114 appears to expose an LDAP service on port 50389.
Early May 2025
- 59[.]110.7.32 exposes an unknown service presenting a Cobalt Strike-generated TLS certificate.
May 7, 2025
- 47[.]120.61.164 presents the same TLS certificate as 59[.]110.7.32 and also exposes a separate Cobalt Strike listener with an active beacon on port 80.
May 13–14, 2025
- The same Cobalt Strike-generated TLS certificate is observed on 152[.]136.165.180 and 49[.]232.102.73, both of which expose Cobalt Strike services without a retrievable beacon configuration.
June 2025
- 124[.]222.137.114 briefly exposes Cobalt Strike listeners on ports 9999 and later 23333, with no observable beacon configuration.
August 18, 2025
- 95[.]179.213.0 exposes SSH on port 22 and HTTPS on port 443, presenting a Cloudflare-style origin certificate issued for bechugh[.]top.
August 20, 2025
- 95[.]179.213.0 takes both SSH and HTTPS services offline.
August 31, 2025
- 95[.]179.213.0 reappears with SSH on port 22 and HTTP on port 8080, again presenting a lazerpenguin[.]com TunnelBear certificate.
September 24, 2025
- 124[.]222.137.114 loses most externally visible services and goes fully dark.
September 29, 2025
- 95[.]179.213.0 exposes a new NTP service on port 123 and an SSH service on port 22 with a new host key.
October 7, 2025
- 124[.]222.137.114 exposes Asset Reconnaissance Lighthouse (ARL) on port 15003.
January 8, 2026
- 95[.]179.213.0 exposes SSH on port 22 and HTTPS on port 8082, presenting another lazerpenguin[.]com certificate.
January 28, 2026
- 47[.]120.61.164 exposes an HTTP-based open directory on port 8090 containing JNDI exploitation artifacts, reconnaissance results, and a whoami.jsp script.
Indicators & Pivots
| Type | Indicator | Context | Link |
|---|---|---|---|
| IP | 124[.]222.137.114 | Asset Reconnaissance Lighthouse (ARL) | View @ 2025-10-07 |
| IP | 124[.]222.137.114 | Cobalt Strike (no beacon) on 9999 | View @ 2025-06-08 |
| IP | 124[.]222.137.114 | Cobalt Strike (no beacon) on 23333 | View @ 2025-06-29 |
| IP | 124[.]222.137.114 | Java Chains exploit service | View @ 2025-02-02 |
| Type | Indicator | Context | Link |
|---|---|---|---|
| IP | 95[.]179.213.0 | Malicious GUP.exe hosting | View @ 2025-02-12 |
| IP | 95[.]179.213.0 | HTTP + OpenVPN w/ lazerpenguin cert | View @ 2025-04-13 |
| IP | 95[.]179.213.0 | Fake Cloudflare origin cert (bechugh[.]top) | View @ 2025-08-18 |
| IP | 95[.]179.213.0 | SSH + HTTP | View @ 2025-10-15 |
| IP | 95[.]179.213.0 | HTTPS on 8082 w/lazerpenguin cert | View @ 2026-01-08 |
| Type | Indicator | Context | Link |
|---|---|---|---|
| IP | 61[.]4.102.97 | Chrysalis C2 (api.skycloudcenter[.]com) | View @ 2025-09-04 |
| IP | 61[.]4.102.97 | C2 TLS cert rotated | View @ 2025-10-16 |
| IP | 160[.]250.93.48 | Pivot via Chrysalis TLS cert reuse | View @ 2025-12-04 |
| Type | Indicator | Context | Link |
|---|---|---|---|
| IP | 59[.]110.7.32 | Loader 1 – open directory | View @ 2025-03-18 |
| IP | 59[.]110.7.32 | Cobalt Strike (no beacon) on 17777 | View @ 2025-05-07 |
| IP | 59[.]110.7.32 | Cobalt Strike (beaconed) on 80 | View @ 2025-05-22 |
| IP | 59[.]110.7.32 | Cobalt Strike on 8999 | View @ 2025-11-03 |
| Type | Indicator | Context | Link |
|---|---|---|---|
| IP | 47[.]120.61.164 | Pivot – shared CS TLS cert | View @ 2025-05-07 |
| IP | 47[.]120.61.164 | CS beacon on 80 | View @ 2025-05-07 |
| IP | 47[.]120.61.164 | Open directory w/ JNDI tooling | View @ 2026-01-28 |
| Type | Indicator | Context | Link |
|---|---|---|---|
| IP | 152[.]136.165.180 | Pivot – shared Cobalt Strike TLS certificate | View @ 2025-05-13 |
| IP | 49[.]232.102.73 | Pivot – shared Cobalt Strike TLS certificate | View @ 2025-05-14 |
| Type | Indicator | Context | Link |
|---|---|---|---|
| CERT | 97fd6268434627a360fa19e6da8fb1d3ccba798ea1a164557a918a8d1073adbe | lazerpenguin[.]com cert used on 95[.]179.213.0 | View Certificate |
| CERT | b16d27408435de623ef6c21e516ba5e28eeac8318bd9146bf7abf57be462faca | lazerpenguin[.]com cert reused | View Certificate |
| CERT | d72b339a6d8f27ae5e1d46584d8432664e59453a60d805c8d78f66669e5cba7e | lazerpenguin[.]com cert (8082) | View Certificate |
| CERT | c533d934f456e390996d795a6dcc06ab3263a36b55f69593a5ba7418f5b0772f | Fake Cloudflare origin cert (bechugh[.]top) | View Certificate |
| CERT | 64f966e99957c7f34768b69aef7a204ebbfaeb68f311c026b4ab84c02ca06ff6 | Chrysalis C2 cert (skycloudcenter[.]com) | View Certificate |
| CERT | 2db0e1bc37978534c0b361eaecf9baf524e7d040b3a5bd4abeafcbedbec9623d | Rotated Chrysalis cert | View Certificate |
| CERT | b9b62d820b366252df21dfa231f3e5f8d491a783ff789cc1e40eea98b374c3e4 | Shared Cobalt Strike-looking cert | View Certificate |
| CERT | 711f15adac78ad62baf0420b24b6bae7b7fcb95f016c94f7ebbbb8065b0341f8 | CS cert (pivoted) | View Certificate |
| CERT | 3dab3b3d4b366b1b80d930b0105254d6d17721ded718078c5372b66731915fb9 | CS cert on Loader 2 | View Certificate |





