Vshell is a Go-based remote administration tool that provides post-compromise capabilities for network pivoting and proxying. While the project is marketed as non-malicious, publicly available project materials have referenced offensive tradecraft (e.g., screenshots involving Mimikatz), and the tool has been observed in unauthorized contexts as a means of remote server management.
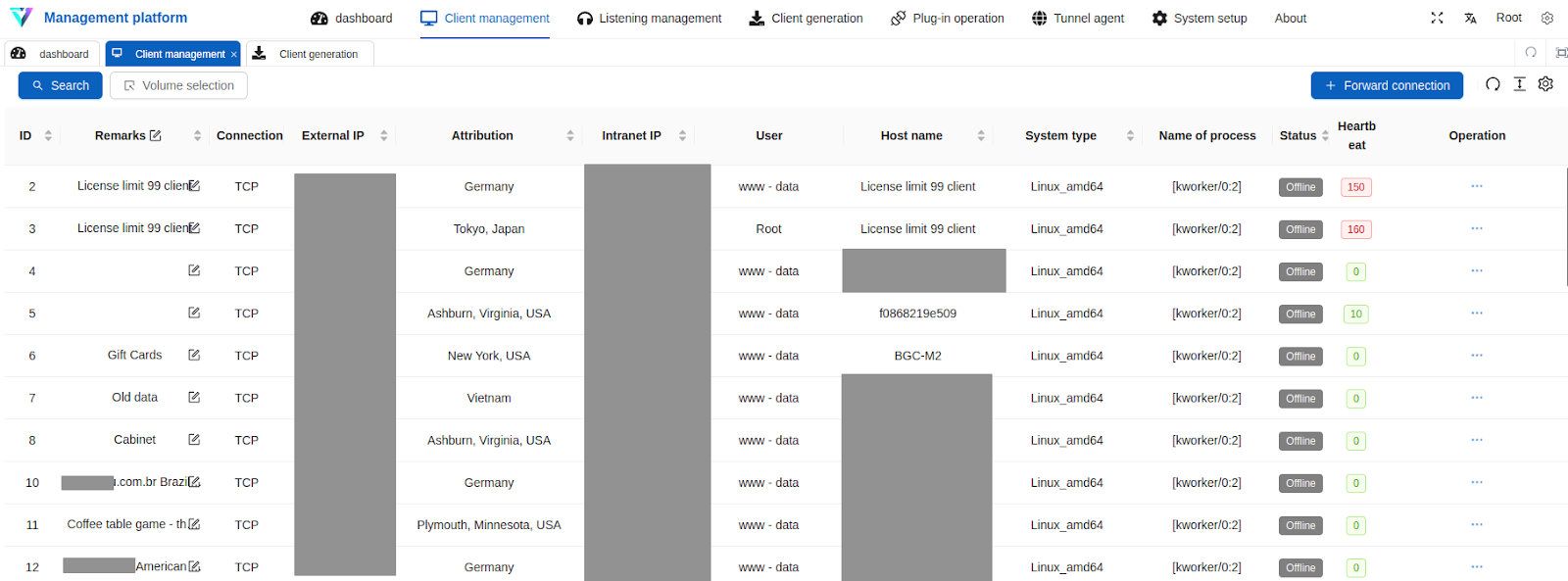
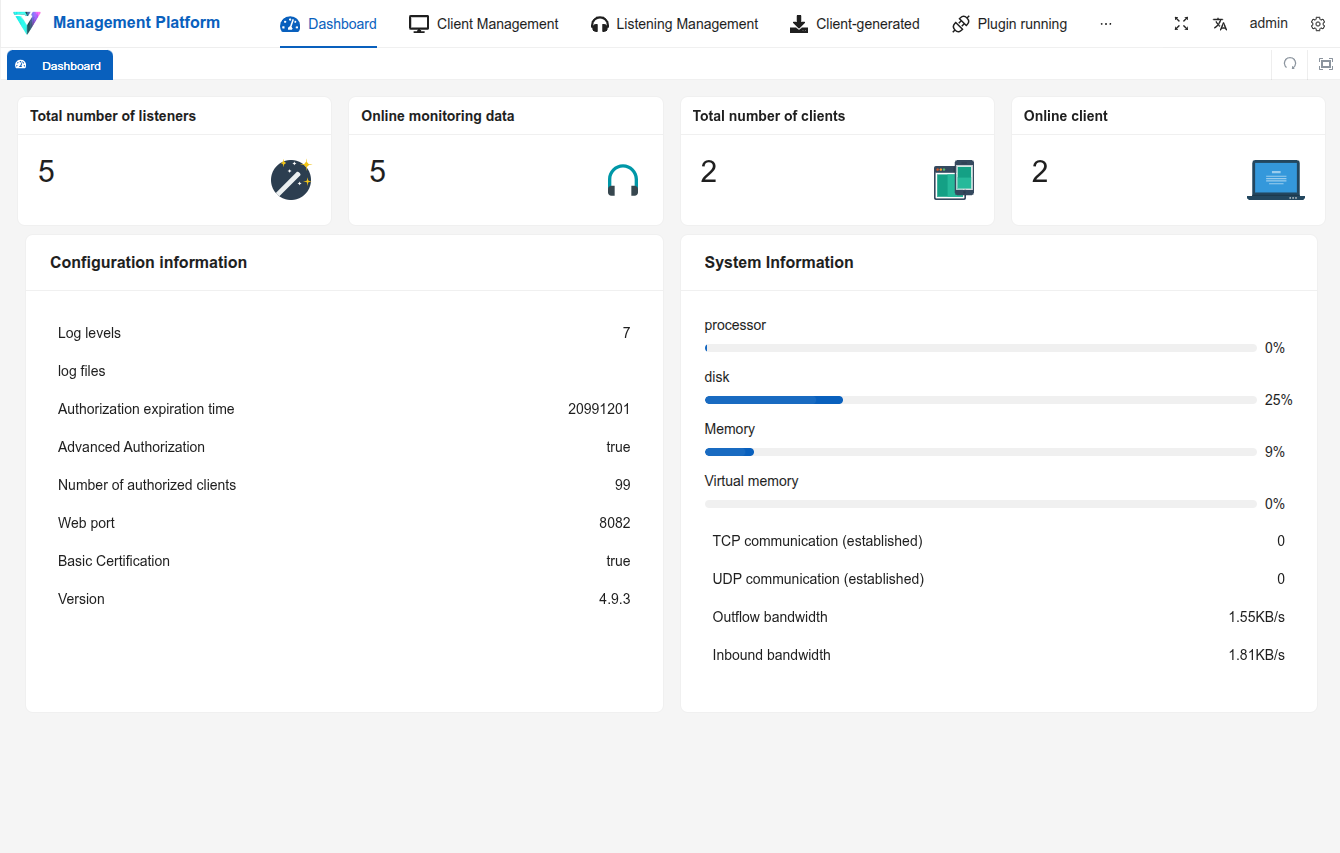
Its distribution model has varied by version, with some releases available as open source and others provided in closed or partially closed form. Internet-facing instances identified via Censys have appeared alongside other common intrusion and red-team tooling such as the commercial adversary simulation tool Cobalt Strike; additionally, exposed web directories have revealed Vshell deployments configured with hundreds of client agents, each of which could be leveraged as a traffic relay for lateral movement and operational proxying. A screenshot of a Vshell panel recovered from an open web directory with 286 attached clients is shown below:
Starting in 2022, Vshell rebased itself onto the intranet penetration proxy NPS, and overlaps between the two toolkits should be expected.
Introduction
Fundamentally, Vshell is a full-featured command-and-control (C2) platform for administering Windows and Linux hosts, with an emphasis on post-compromise host management and network pivoting. Vshell is commonly seen within Chinese-speaking offensive-security ecosystems, with users ranging from researchers to red teams as well as threat actors. Release descriptions of Vshell originally called it a RAT (remote access tool), while later versions positioned it as an approachable alternative to commercial adversary-simulation frameworks. The tagline for version 3 reads: “CobaltStrike难用?来试试vshell吧” (translation: “Is Cobalt Strike difficult to use? Try Vshell instead!”).
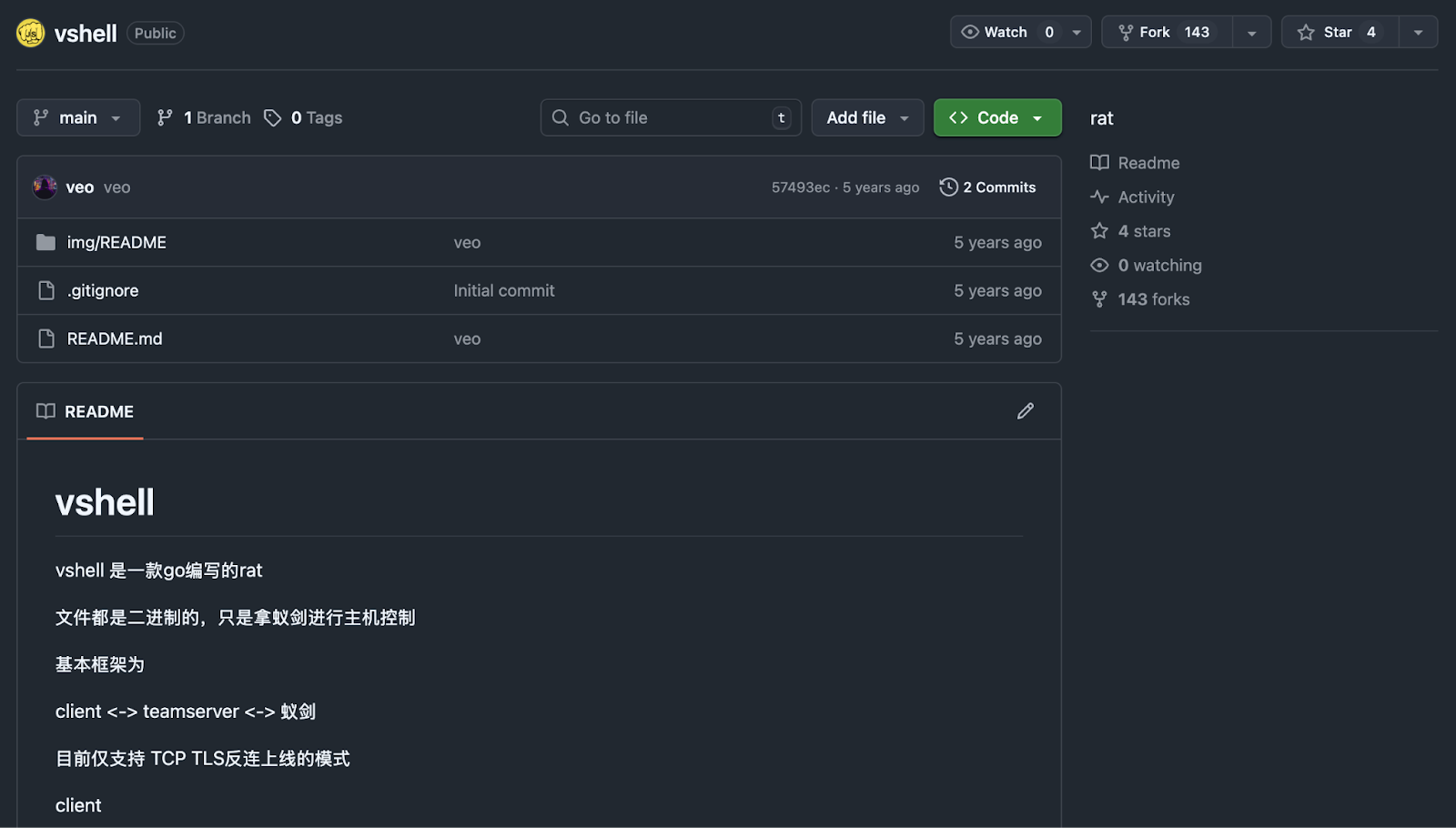
Throughout Vshell there is clear inspiration from CobaltStrike. Vshell follows the same logical C2 architecture: a centralized server (“teamserver”/controller) that manages implants (clients) and provides an operator interface. Early iterations (circa 2021) exposed a web API, and operators reportedly relied on 蚁剑 (AntSword) for operational usage.
Reporting from NVISO provides an excellent outline of the history of Vshell. Based on their reporting, Vshell has had 5 significant milestones in its development:
| Version | Year | Description |
| v1 | 2021 | Vshell’s main component was called “teamserver”, no user interface and was designed controlled by AntSword. |
| v2 | 2022 | Local web interface |
| v3 | 2022 | Vshell’s implements NPS for network protocol and forks frontend |
| v4 | 2023 | Licensing, interface redesign, nginx impersonation and additional protocols |
| v4.6 | 2024 | End of public releases, suspected private development |
During 2025, Vshell was reportedly used within several incidents, such as Operation DRAGONCLONE, SNOWLIGHT campaign from UNC5174, and in August, Trellix reported on a phishing campaign leveraging Vshell.
The following section summarizes Censys visibility into infrastructure and prevalence trends associated with Vshell.
Technical Characteristics
Internet-facing Vshell deployments observed by Censys periodically appear in open web directories and are seen in our continuous scanning. In exposed instances, operators are commonly seen using copies of Vshell v4, which supports both Windows and Linux clients (including x86_64 and ARM variants).
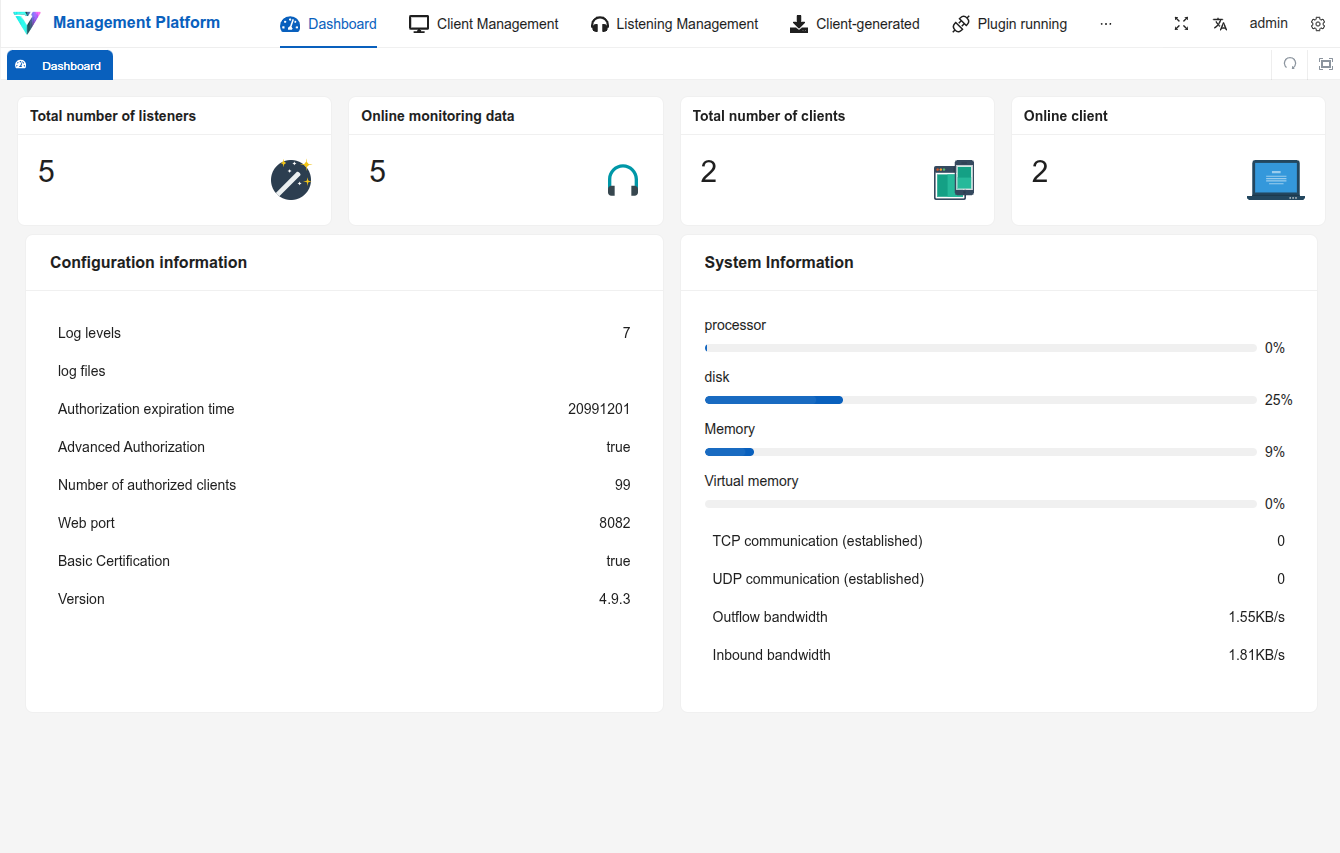
The interface is natively shown in Mandarin. The screenshots below show a test instance we deployed for our analysis, first in the original Mandarin and then translated into English.
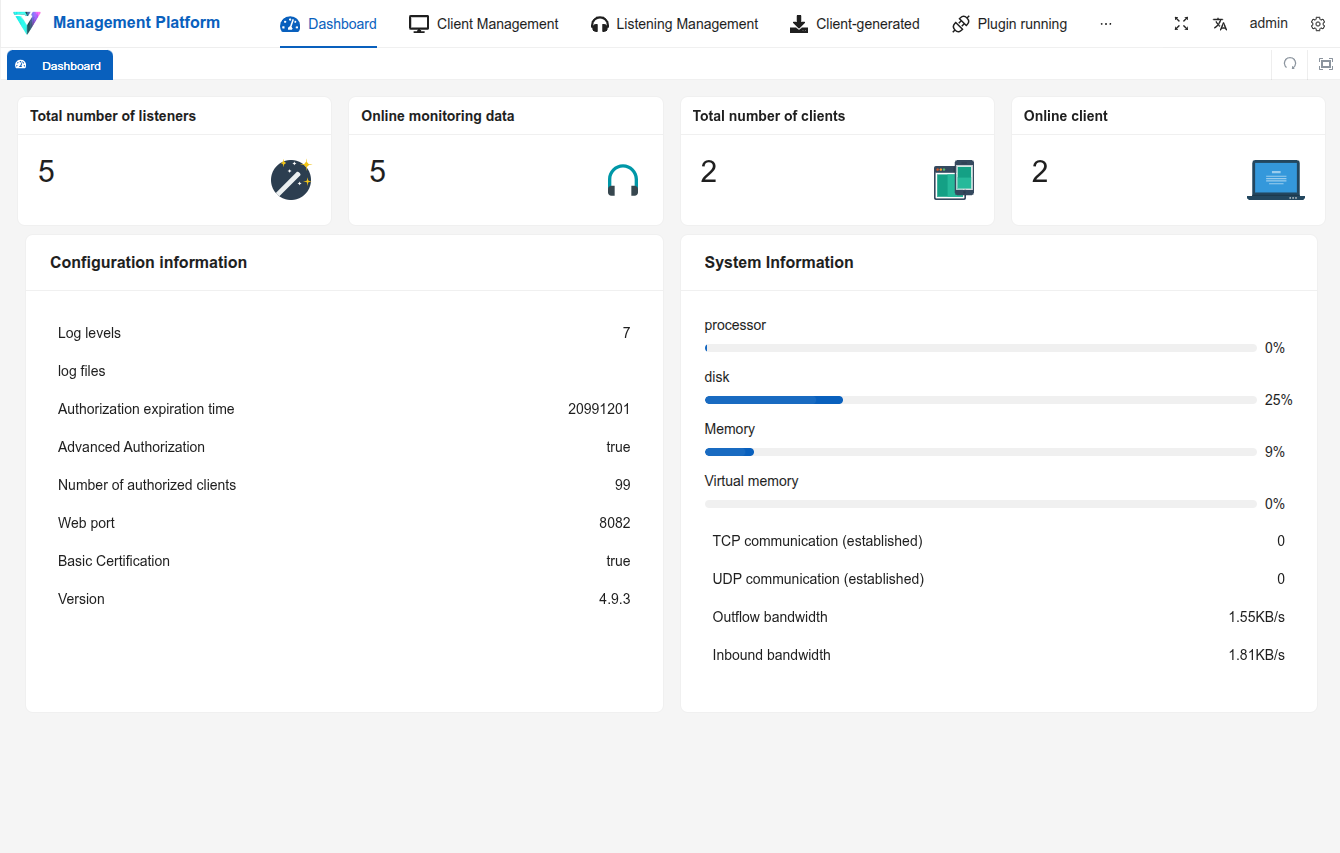
Vshell uses “listeners,” which are the service components within the controller that accept inbound connections and manage communications with deployed clients; these are configured in through 监听管理 (“Listener Management”). Service configuration varies across deployments; however, several of the listener services within Vshell default to port TCP/8084. The operator creates a listener by selecting the transport/protocol and specifying connection parameters (for example, bind address/interface, port, and any authentication or encryption options presented by the UI). Once enabled, the listener remains available to receive new client sessions and to broker tasking, data transfer, and tunneling features through the established channel.
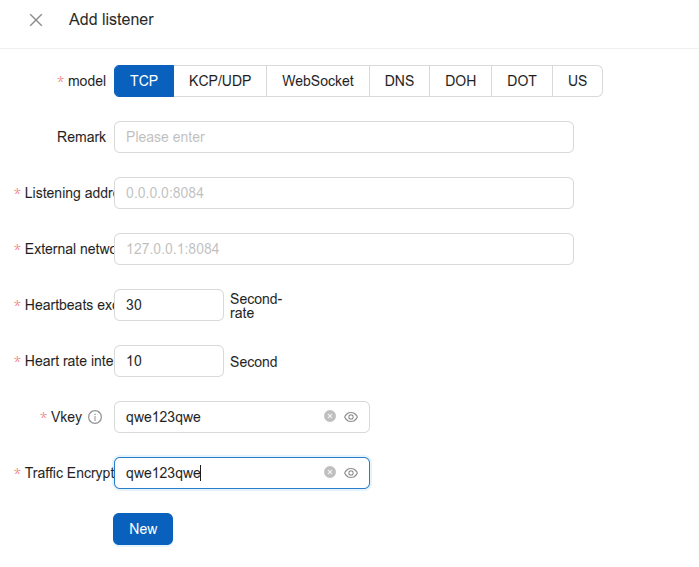
The following screenshot shows the form for creating a new listener in Vshell:
Vshell supports multiple listener types, each with distinct settings and operator-facing labels. The following table shows default bind addresses shown when creating a new listener.
| Listener Type | Default address | Description |
| TCP | 0.0.0.0:8084 | Communication over UDP |
| KCP/UDP | 0.0.0.0:8084 | Communication over TCP |
| WebSocket | ws://0.0.0.0:8084/ws | C2 using HTTP Websockets |
| DNS | 0.0.0.0:53 | C2 over DNS |
| DOH | 0.0.0.0:53 | DNS-over-HTTPS |
| DOT | 0.0.0.0:53 | DNS-over-TLS |
| OSS | S3 bucket URL | Object Storage System (S3) |
The range of listeners illustrate Vshell’s emphasis on flexible and varied communications. For defenders, this means Vshell has multiple points for detection, instead of just a single port or protocol fingerprint.
Censys Perspective
Censys Threat Hunting module customers can identify Internet-facing Vshell exposure, using the following query:
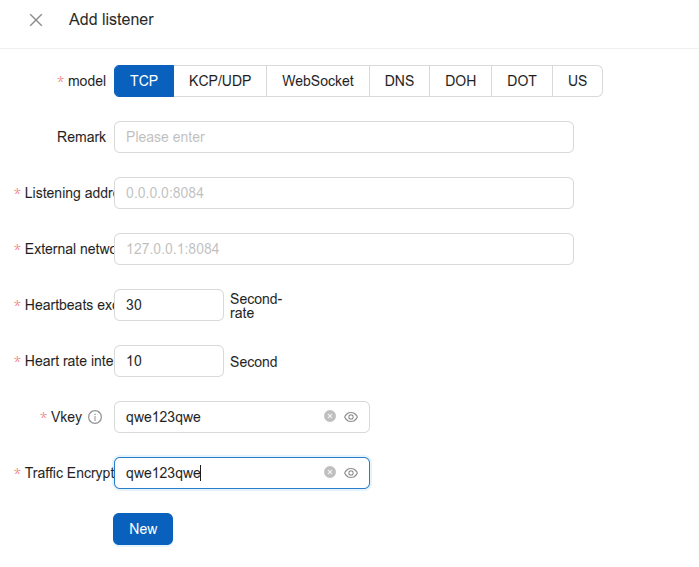
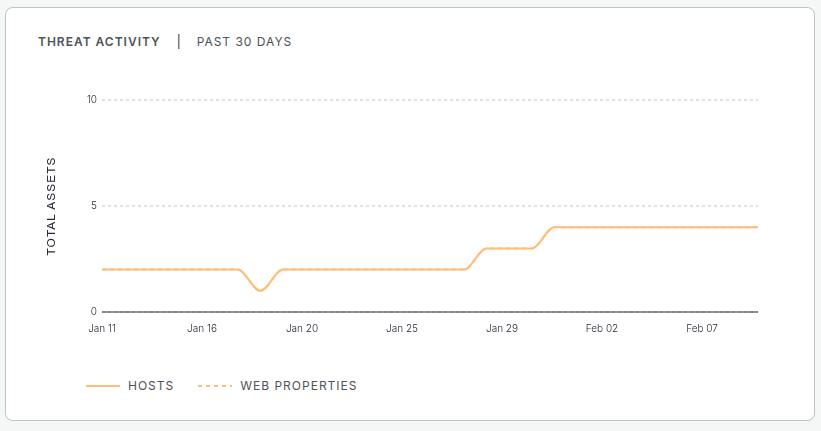
host.services.threats.name = "Vshell" or web.threats.name = "Vshell"On average, we at Censys often only see a small subset of the older panels still online, typically under 5 instances at any given time:
Older panels often present fingerprintable artifacts that can support identification and historical tracking, such as copyright markings, which were more common in earlier releases and are useful for retrospective analysis. An example of an older Vshell panel is shown below:
Newer panels have moved to digest authentication, which reduces the number of fingerprintable detection opportunities. Despite this, at the time of this report, we see over 850 of the listeners for Vshell in our scanning:
Vshell exposure should be interpreted as part of a wider pattern Censys routinely observes within dual-use post-compromise frameworks: operator tradecraft tends to reduce fingerprintable detection surfaces over time, while keeping the minimum necessary network services reachable for session management and pivoting.
Takeaways
Vshell is a mature post-exploitation capability. The combination of capabilities, availability and cross platform functionality make it a popular option for Mandarin speaking adversaries.
Defenders should monitor for Vshell as a potential tool threat actors may leverage for establishing a foothold on their network — especially around external facing infrastructure such as web servers and firewalls. As Vshell is built on NPM, detection rules may overlap in some instances.
Leverage the Censys Threat Hunting Platform to identify and disrupt infrastructure linked to Vshell. Run the provided queries regularly and alert on any outbound communications matching these patterns.