SOC teams are under pressure to modernize: faster triage, better investigations, and more consistent outcomes. Many SOC enrichment and SOC optimization efforts fail for a simple reason: analysts are forced to assemble “Internet context” by hand, across point tools and stale feeds.
That’s not a capability gap. It’s a workflow tax.
This post is about reducing that tax without fear, hype, or pretending security is simple. The goal isn’t to “solve security.” It’s to make the parts that are reliably repeatable — like understanding what’s actually online — more evidence-based and less swivel-chair. Give that chair a break before the hydraulics explode!
The key to smoother workflows lies in establishing a ground truth layer to your data.
The “Simple but Effective” Reality of Security Operations
Your SIEM and SOAR playbooks, AI automation, threat hunting, and incident scoping must start from reality — and reality means really good data.
Kelly Shortridge’s annual DBIR sensemaking is a good reminder that breach data is useful but incomplete, and that we should be skeptical about what it can and can’t tell us. She also calls out a trap we all fall into: getting excited about “new shiny data” without translating it into impact, tradeoffs, and decisions.
One of her strongest points: defenders sleep on “boring” attack patterns — namely stolen credentials — because they’re not resume-fodder. Even though they work, and scale. She also urges readers to look less at year-over-year whiplash and more at longer-term patterns.
That framing matters for how you should think about Internet context tools.
Most SOC investigations don’t start with a rare zero day and a perfectly labeled actor. They start with messy indicators:
- an IP from an identity provider alert
- a domain in proxy logs
- a certificate fingerprint from EDR telemetry
- a service banner surfaced during triage
- “is this ours?” from a panicked Slack message
Your success comes from moving quickly, in as few consoles as possible. Clue, evidence, decision.
Where Censys Helps: More Evidence, Less Manual Assembly
Censys Platform helps SOCs act efficiently by providing a ground truth layer: first-party Internet visibility, freshness and history, and research-curated context tied directly to hosts, services, certificates, and domains. Think of Censys as the external reality layer your internal tools don’t naturally have.
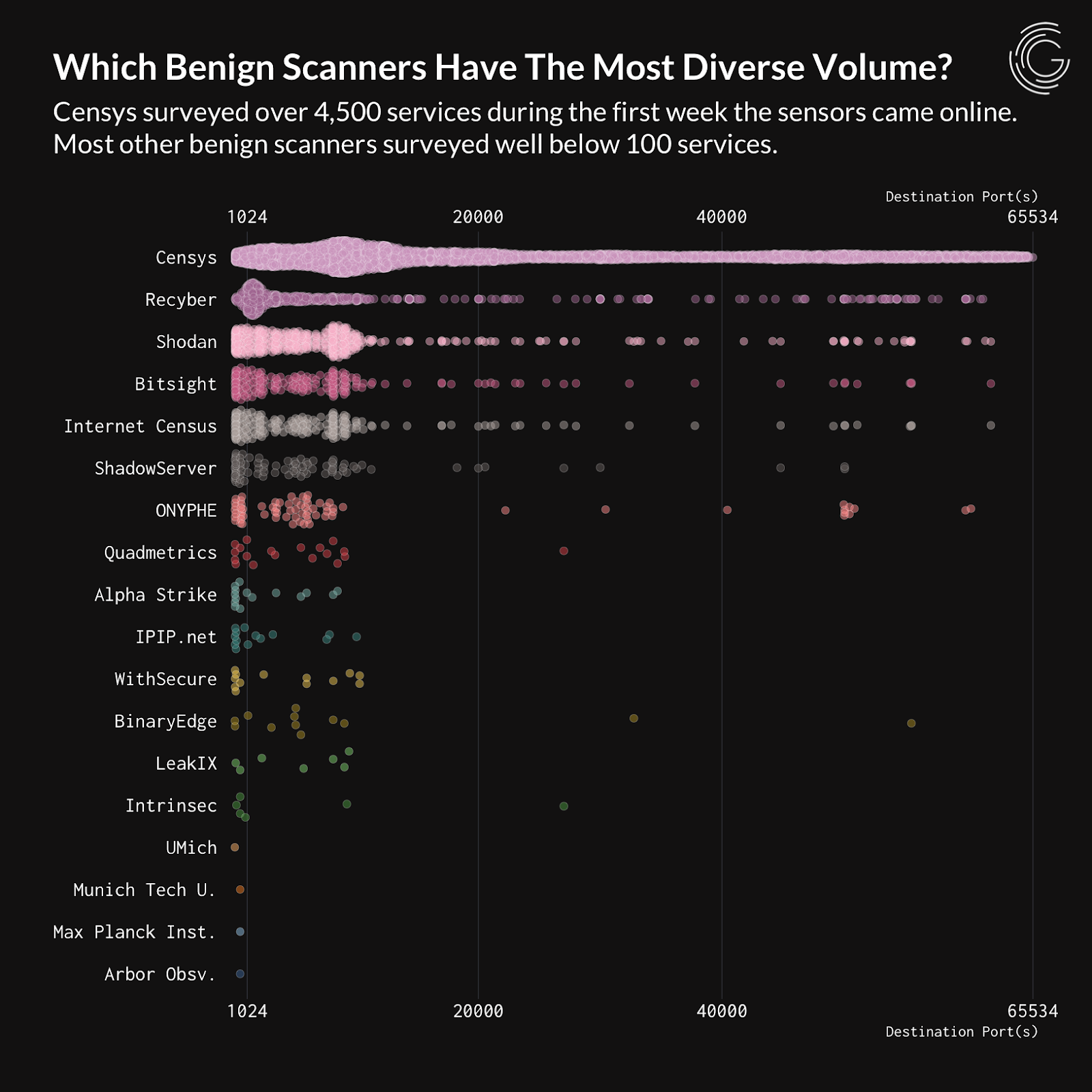
1) First-party Internet data (not stitched aggregation)
Censys scans and maintains its own Internet Map. That matters. When data is stitched from many sources, you inherit uneven coverage, inconsistent identifiers, and “it depends” caveats that analysts only discover mid-incident.
2) Freshness and history, together
Freshness answers: what is it serving right now?
History answers: what was it serving when the incident happened?
That second question is where investigations bog down. Analysts argue about whether an exposure “was real” or “must have been transient,” because they only have yesterday’s snapshot.

3) Raw signals and opinionated enrichment in the same workflow
You want the raw evidence (services, certs, domains, host details) and the security-ready interpretation (threat tags, vulnerability intelligence, campaign/C2 context) tied to the exact entity you’re working on. No copy/pasting across tabs.
4) Plugs into your existing security stack
Shortridge’s “so what” critique is basically a demand for operational utility. In short: does it show up where we work already? Censys is designed to enrich SIEM/SOAR/TIP workflows and internal tooling, to deliver real-time external Internet context automatically and consistently.
5) A platform that is built for practitioners
Incidents are ambiguous, time-constrained, and never as clean as what you see in demos. Censys knows this and continues to deliver capabilities like CensEye pivots, an investigation assistant, researcher-curated rapid response queries, and the tools that help you in the real-world.
Three SOC Playbooks
SOC L1 triage: “What is this simplistic alert in my SIEM?”
Trigger: Alert contains IP/domain/cert hash.
Goal: Quickly decide whether this is misconfig, commodity abuse, or something that deserves escalation.
Censys adds:
- what the host is actually serving right now (services/ports/banners)
- related certificates and domains (pivot points)
- vulnerability context relevant to exposed services
- threat labels / detections attached to the entity
Why it helps: Analysts stop burning cycles reconciling contradictory enrichment, and instead move straight to evidence-backed next steps.
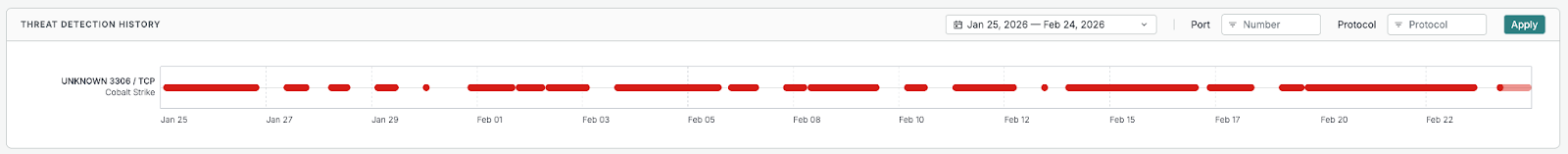
Incident Response: “Does the history change my incident scoping?”
Trigger: “Was this exposed last week?” / “Did the cert rotate after compromise?”
Goal: Establish a timeline you can defend.
Censys adds:
- historical observations for services/ports/certs/domains
- timeline views and change over time (appearance/disappearance, rotations, new associations)
Why it helps: You spend less time debating and more time measuring. This is the kind of “impact-aware” work Shortridge is pushing for: tie decisions to tangible reality, not vibes.
Threat Hunting: “Show me adjacent infrastructure.”
Trigger: One clue (patterned hostname, shared cert, exposed admin panel, particular service fingerprint).
Goal: Find related infrastructure clusters fast.
Censys adds:
- pivots across certs, hosts, domains, services
- threat and vulnerability labels curated by our security researchers–tracking active campaigns and frequently publishing findings
Why it helps: You avoid overfitting to one IOC and instead hunt for the shape of activity.
Consolidation Without the “Replace Everything” Fantasy
If your team is stitching together “what’s online” from one vendor, “what it means” from another, and “is it ours / is it changing” from a third, you pay a tax in time and missed signal. Censys can collapse that Internet-context layer into one workflow: broad discovery, freshness, history, and enrichment tied to the exact indicators you’re investigating.
And it still complements what you already run.
Censys isn’t trying to be your SIEM, EDR, or your entire threat intel program. It’s the ground-truth layer that makes those systems sharper. It’s a reduction in friction, so your analysts can spend their limited attention on decisions that matter.
Censys already fuels everything from Verizon DBIRs to ISAC briefings and bulletins. Now let it fuel your investigations and triage. Learn more about how Censys powers the SOC, or request a demo to start exploring how Censys can streamline your SOC workflows.