Understanding which ports and protocols are exposed across your digital environment is no longer optional; it’s essential. With attackers increasingly exploiting non-standard ports to evade detection, security teams need faster, clearer insight into their exposure footprint.
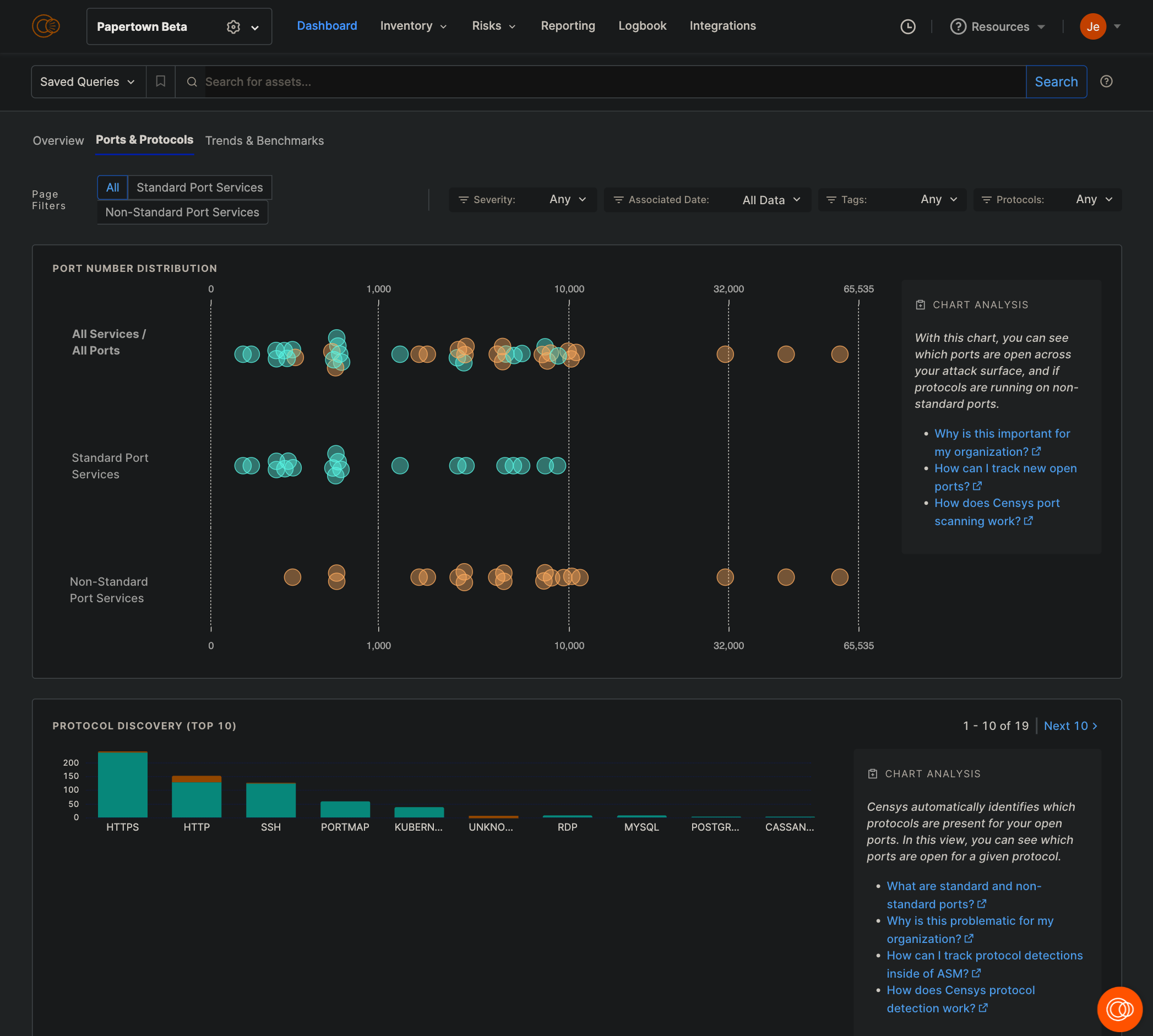
That’s why we built the Ports & Protocols Dashboard — an intuitive, high-impact feature within Censys Attack Surface Management (ASM), powered by the most comprehensive, continuously updated Internet Map in the industry. This map, unique to Censys, enables unmatched visibility into your external attack surface, across all 65K+ ports, in near real-time.
The dashboard is built to deliver complete coverage, accurate classification, and most importantly, relevant insights that help security teams focus on the exposures that matter most. It filters noise and surfaces actionable intelligence, so defenders can address what’s open, what’s risky, and what needs attention now.
With the Ports & Protocols Dashboard, security teams gain immediate clarity into where risk lives, where compliance may be failing, and where misconfigurations leave the door open to attackers.
From raw data to relevant intelligence
The Ports & Protocols Dashboard addresses these challenges head-on. It delivers a clear, intuitive view of your organization’s exposed services — not just which ports are open, but what protocols are running on them, and how those services align with compliance requirements and threat models.
Because it’s built on the Censys Internet Map, refreshed daily, the data is timely and reflective of your actual exposure, not a point-in-time snapshot. Security teams can detect unusual patterns, like HTTPS traffic on high-numbered ports, that may signal misconfigurations or active compromise.
But what makes the dashboard truly powerful is its ability to surface relevant data. It’s not just dumping open port lists, it contextualizes them. Is the service expected? Is it associated with a known asset? Is it flagged by policy or compliance baselines? That kind of intelligence empowers SOC analysts and vulnerability managers to prioritize issues that carry real risk, instead of chasing down noise.
Each data point links directly to rich inventory context in Censys ASM, including ownership, geographic location, related domains, service history, and known vulnerabilities.
Making compliance and remediation manageable
Security leaders are under pressure to prove alignment between policy and reality. Whether preparing for a third-party audit or demonstrating due diligence to the board, having a defensible, up-to-date view of your port and protocol landscape is now a baseline requirement.
The dashboard streamlines this by showing where exposures deviate from standard configurations and where exceptions may indicate a policy failure or asset drift. This reduces the time it takes to detect misconfigurations, shortens remediation cycles, and helps teams close compliance gaps before they become audit findings or real-world breaches.
What used to be a tedious, cross-referenced task has become a seamless, interactive process grounded in accurate and complete internet-wide visibility.
See what you’ve been missing
The Ports & Protocols Dashboard is now live in Censys ASM. If you’ve ever wondered what your organization is exposing, and whether it’s what you meant to expose, now’s the time to find out. This is visibility that’s Complete, Accurate, Relevant, and Timely, and it’s built to help you take back control of your external exposure, one port at a time. Explore Censys Attack Surface Management here.