Zero days attract a huge amount of attention in the security community, an amount that is completely disproportionate to how many of these vulnerabilities emerge each year and how often they’re actually used in attacks. They’re the Cybertrucks of security. They’re famously bad, but aren’t actually used very often.
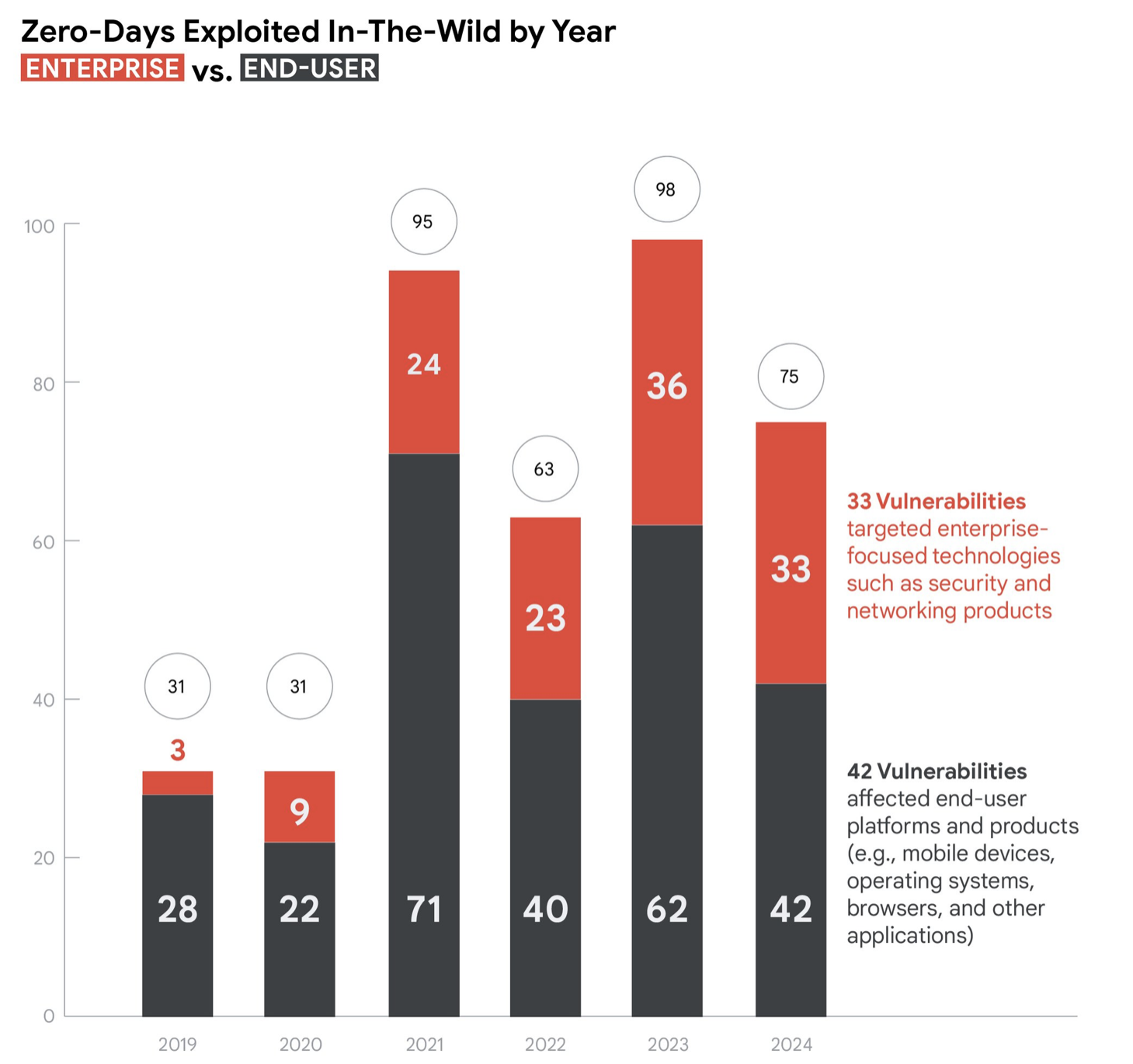
But zero days are still out there, and new data compiled by Google Threat Intelligence Group shows that while the total number of zero days identified in 2024 dropped to 75 from 98 the year before, more of those vulnerabilities are in enterprise products now, and most (60%) of those are in security and networking products. That won’t come as a surprise to enterprise defenders who have spent the last couple of years responding to critical vulnerabilities in firewalls, VPN appliances, and routers. In 2024, there were 33 zero days discovered in enterprise-focused products, slightly fewer than the 36 discovered in 2023, but those 33 bugs represent 44% of the total zero days in 2024, as opposed to 37% in 2023.
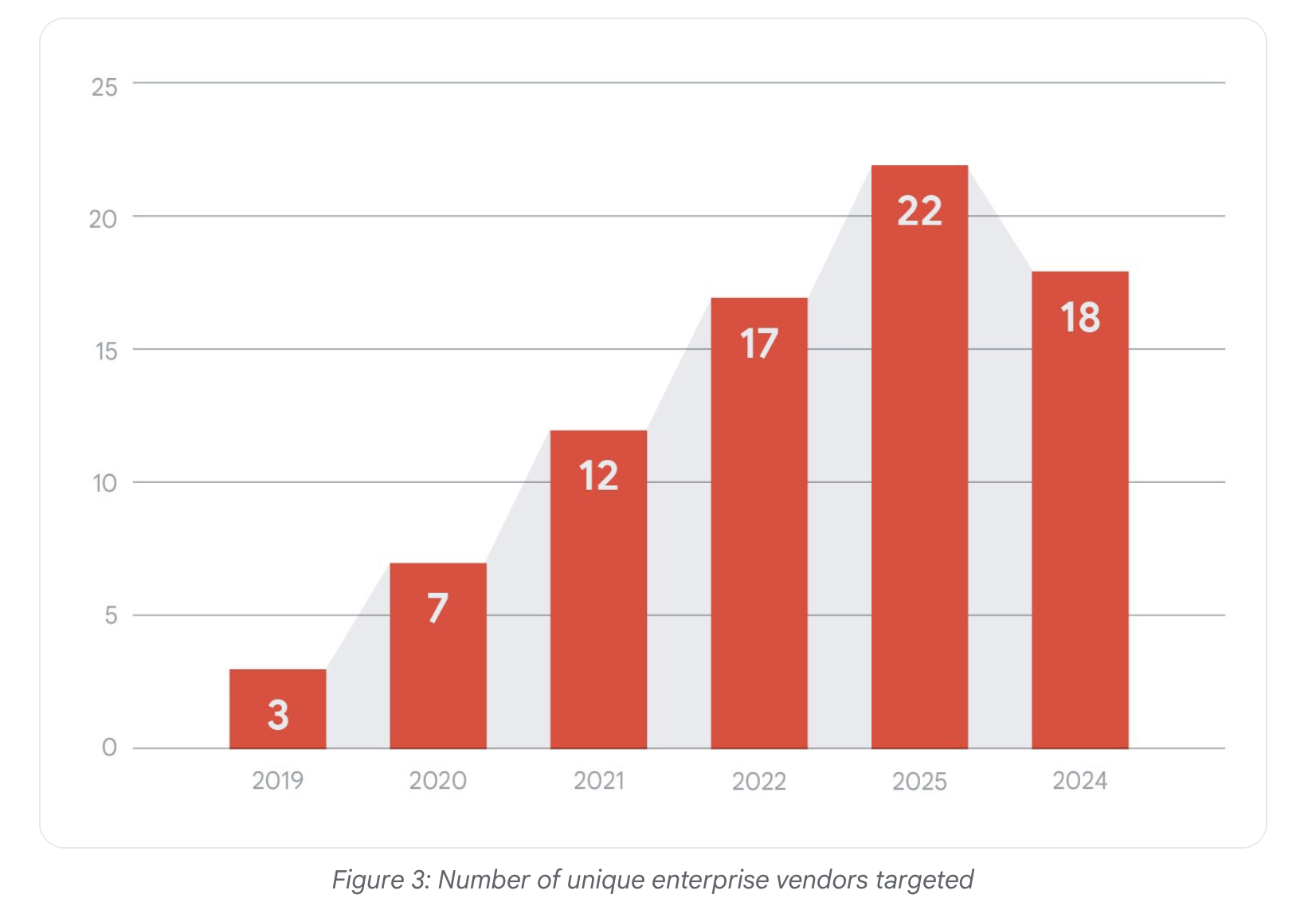
“Over the last several years, we have also tracked a general increase of enterprise vendors targeted. In 2024, we identified 18 unique enterprise vendors targeted by zero-days. While this number is slightly less than the 22 observed in 2023, it remains higher than all prior years’ counts. It is also a stark increase in the proportion of enterprise vendors for the year, given that the 18 unique enterprise vendors were out of 20 total vendors for 2024,” Google’s researchers said in their report on the data.
From an attacker’s perspective it makes perfect sense to target enterprise products, especially networking and security appliances. Those devices can grant a successful adversary broad access to the target organization, and there are often many different options to choose from when attacking a router or firewall. Bugs abound. Cisco, Ivanti, Palo Alto Networks, and other vendors have all had their share of zero days to deal with recently.
At any given time, an attacker sitting down at the keyboard to do a little light hacking has an absolute embarrassment of known vulnerabilities to choose from. So many bugs, so little time. So many, in fact, that there’s no practical reason for most threat actors to do their own vulnerability or exploit development. The main exceptions to that rule are state-backed actors and the commercial surveillance vendors (CSV) that sell intrusion technology to law enforcement agencies and governments.
“Although the total count and proportion of zero-days attributed to CSVs declined from 2023 to 2024, likely in part due to their increased emphasis on operational security practices, the 2024 count is still substantially higher than the count from 2022 and years prior. Their role further demonstrates the expansion of the landscape and the increased access to zero-day exploitation that these vendors now provide other actors,” the Google researchers said.
Adversaries are continuing to hone their craft, especially at the higher end of the spectrum, but defenders and vendors are making strides, as well, learning from past attacks and adjusting their tactics. Expect both trends to continue as the back-and-forth struggle evolves.
Images from Google Threat Intelligence Group report