In today’s tech landscape, securing your web infrastructure isn’t just about throwing out certificates and then dusting off your hands. You need to know who else might be issuing them to pretend they’re you. Someone attempting to fraudulently create legitimate-looking certificates can distribute malware, conduct Business Email Compromises or hit you with a wholesale data breach. That’s where Certificate Transparency (CT) logs might be the friend you didn’t know you needed.
How Does Certificate Transparency (CT) Work?
Introduced by Google in 2013 in response to the DigiNotar breach of 2011, and part of an open framework called Certificate Transparency, CT logs provide a public, auditable record of all certificates issued by publicly trusted Certificate Authorities. At Censys, we think that monitoring CT logs for domains you have a blood oath to protect is a crucial practice for any organization that values trust, security, and oversight of its digital identity.
Every time a Certificate Authority (CA) issues a new certificate, it’s recorded in a public CT log. These logs act as a public ledger, allowing anyone to verify that a certificate exists, and that it was issued appropriately. The problem is, do YOU have time to watch the logs? If not, imagine CCTV cameras beaming onto screens in a security office where the guards are permanently at lunch. Sure, you can look at historical footage, but, by then, you’ve missed all the action.
Key Benefits of CT Monitoring
Catch Malicious Certs
If an unauthorized CA issues a certificate for your domain, it could allow an attacker to impersonate your organisation. Monitoring CT logs gives you early warning, allowing you to quickly work with the CA to revoke the rogue cert.
Faster Incident Response
Real-time alerts from CT monitoring tools reduce the time between a threat emerging and your response. Quick action can prevent phishing, data theft, or damage to your brand.
Shadow IT Detection
Sometimes internal teams spin up services without proper oversight. CT logs can reveal previously unknown services or subdomains, helping you maintain visibility and control. The cert.ever_seen_in_scan:true operator we used above gives you that extra certainty that any malicious, malformed or funky certs have actually been seen on hosts.
Certificate Lifecycle Management
Keeping track of your certificates can be difficult as it is. 90-day lifespans for certs, per Google and Let’s Encrypt is going to compound the problem. CT monitoring can help you maintain compliance and good governance by revealing expiring certs, misconfigurations, or use of weak cryptography.
Audit and Compliance Support
Regulations like PCI-DSS, HIPAA, and SOC2 demand strict control over your cryptographic assets. Monitoring CT logs demonstrates proactive security practices and supports compliance audits.
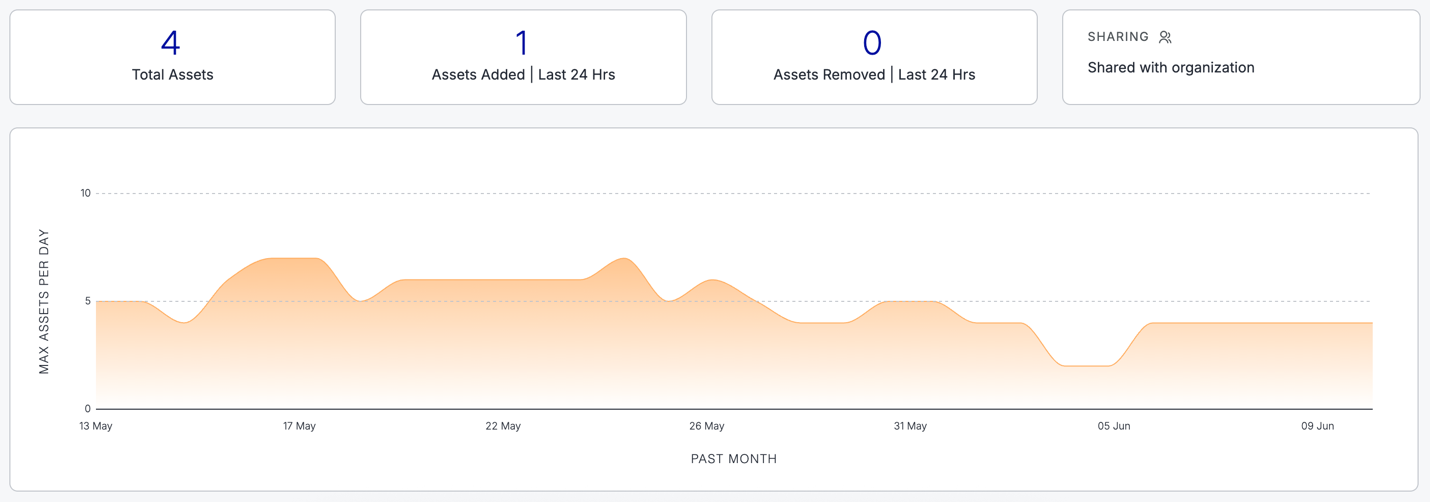
Censys Makes CT Monitoring Easy
One major challenge with leveraging CT data is that it’s spread across multiple systems maintained by different organizations, making it difficult to directly monitor all CT logs that might be relevant to your organization. Fortunately, Censys makes this a simple task by aggregating CT logs into a single database. By watching for certs being created, you can validate their inclusion in the CT landscape and ensure they’re legit and supporting your business, and not the business of hackers.
Try this query in platform.censys.io:
cert.names: "cnn.com" and
cert.parsed.validity_period.not_before >= "now-7d" and
cert.parsed.validity_period.not_before < "now"Try your domain, a wildcard, or even a regex to look for certificates containing typosquat names. Better still, with Censys Platform, you can have this query automated as a Censys Collection, and receive alerts whenever a new certificate is issued – in real-time!

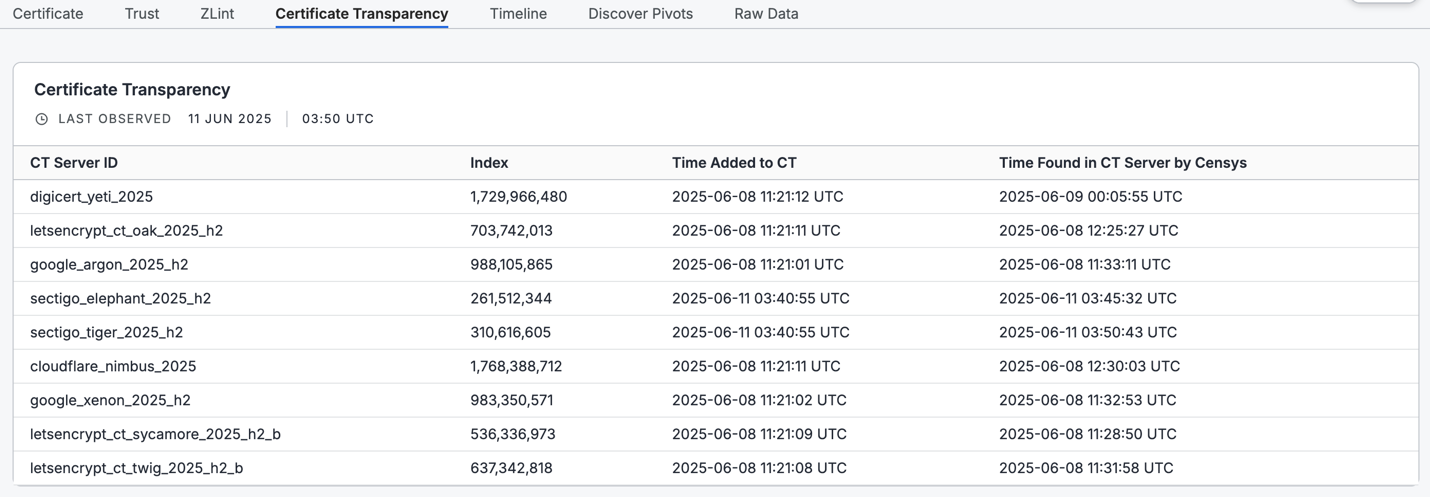
Soon, you’ll even be able to use dnstwist directly in Censys queries. Dnstwist is a domain fuzzer that identifies permutations of a provided domain name, helping you generate a list of lookalike domains that you may want to monitor via CT logs. Check this example out:
dns_twist(cert.names, "paypal.com") and not cert.names:
"paypal.com" and not cert.names=~".*\.paypal\.com” and
cert.revoked: false and cert.ever_seen_in_scan: true and
cert.added_at >= "now-1M"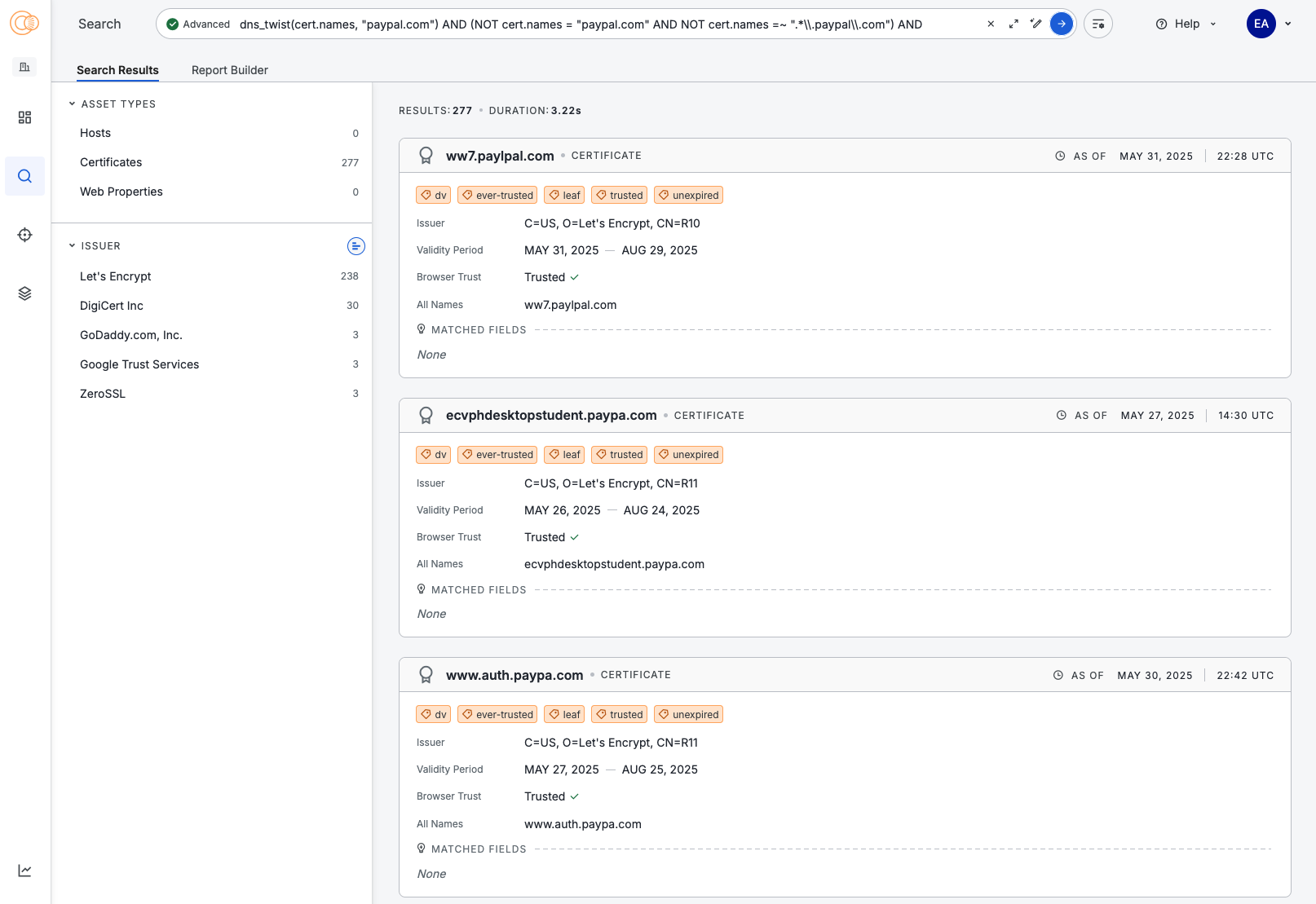
Here’s a sneak peek of what this will look like in Platform. The above query is searching for certificates:
- With Paypal-like names,
- That have been seen in our scans, not just CT logs–meaning the certificate is or has been used on a host at some point,
- That are not currently revoked, and
- That were added in the last month
You can then create a Collection directly from the Search Results page, and you’ll be able to monitor all results in real-time. Collections are available now, and dnstwist is coming to Platform in Q3!
Bottom Line
Monitoring Certificate Transparency logs isn’t just a security best practice—it’s a necessity. It protects your users from fraud, keeps the auditors happy, helps prevent data breaches, and maintains the integrity of all of your online services. Censys Collections do the heavy lifting for you. Create a pattern that represents your domains, create a Collection and sit back and wait for the alerts. Whether you’re a small startup or a global enterprise, implementing Collection-based monitoring for CT logs should be a cornerstone of your certificate governance strategy.
Don’t get bogged down. Let Censys Collections help keep your certificates sparkling clean. Try it today in your Censys Platform account. If you don’t have one, you can get started for free.