Censys ARC has identified a threat actor using non-traditional network transport layers to establish command and control infrastructure. The group, which we track as Pigeon Forge, is the first known APT to operationalize RFC 2549 (IP over Avian Carriers with Quality of Service) for persistent C2 communication. Compromised servers respond exclusively with HTTP 418 “I’m a Teapot”, suggesting that the actors accidentally deployed the Hyper Text Coffee Pot Control Protocol (RFC 2324) instead of standard HTTP.
We are designating this campaign BrewJack.
Discovery
Our team first noticed anomalous activity during routine monitoring of Internet-facing infrastructure in the Ashburn, Virginia metro area. Specifically, a Censys engineer reported an unusual accumulation of organic matter on a datacenter rooftop ventilation unit. Upon closer inspection, each pigeon roosting on the structure was found to be carrying a microSD card in a leg band, with QoS bar-code markings on its wing consistent with Business-class IPoAC service as defined in RFC 2549.
The following image was recovered from datacenter security cameras on the night of the initial breach:

Initial triage of the microSD cards revealed encrypted payloads. After decryption (the pigeons were self-keying, per the RFC), each card contained a single HTTP request destined for compromised infrastructure. Every response we observed carried the same status code: 418 I’m a Teapot.
The threat actors likely meant to deploy standard HTTP but instead shipped a build compiled against the HTCPCP specification. This is supported by the presence of Content-Type: application/coffee-pot-command headers in captured traffic and the fact that several payloads contained the BREW method rather than POST.
Technical Analysis
The following figure summarizes the BrewJack command-and-control path and where protocol confusion enters the stack.
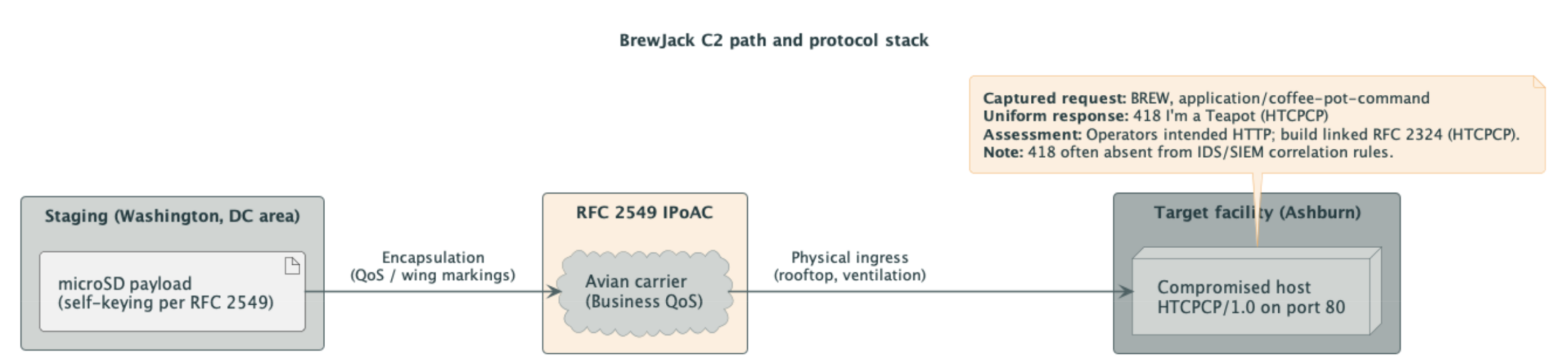
Figure 2: BrewJack C2 path from staging through IPoAC transport to the compromised host. Not to scale; carrier drawn smaller than actual MTU.
Transport Layer
BrewJack’s C2 channel operates entirely over IPoAC. The threat actors built a transport layer that is more elaborate than the medium deserves:
- Carrier class: Business (based on wing bar-code markings), with occasional First-class carriers observed during what we believe are priority exfiltration operations
- MTU: Approximately 32 GB per carrier (microSD capacity), significantly exceeding traditional network MTUs
- Latency: Variable. Our measurements indicate an average round-trip time of 4 to 6 hours, with spikes during migration season
- Packet loss: Estimated at 12 percent, primarily attributed to hawks (unintentional encapsulation, per RFC 2549) and one confirmed incident involving a datacenter cat
The following is a reconstructed packet capture from an intercepted carrier:
Frame 1: 1 pigeon on wire
IPoAC Header:
Version: 2549
QoS Class: Business
TTL: ~15 years
Source Coop: 38.9072° N, 77.0369° W (Washington, DC)
Dest Coop: 39.0438° N, 77.4874° W (Ashburn, VA)
HTCPCP/1.0:
Method: BREW
URI: /pot-1/teapot
Content-Type: application/coffee-pot-command
Accept-Additions: cream;1
HTTP/1.0 418 I'm a Teapot
Content-Type: text/short-and-stout
X-Spout: ready
X-Handle: operational
Malware Behavior
Once a server is compromised by BrewJack, it exhibits the following behaviors:
- All HTTP responses return 418. Regardless of the request method, path, or headers, the server responds with “I’m a Teapot.” That makes the server useless for its intended purpose, and makes most monitoring tools stay quiet because 418 is rarely included in alerting rules.
- The server begins broadcasting HTCPCP service advertisements on port 80, replacing its original HTTP service. Censys observed these services in scan data with the banner HTCPCP/1.0 418 I’m a Teapot.
- A cron job is installed that plays cooing sounds through the server’s audio output at 3 AM local time. We believe this is a carrier homing signal.
Censys Search Query
Affected infrastructure can be identified using the following Censys search query:
host.services.endpoints: (http.status_code: 418 and http.headers.value: "HTCPCP")At the time of publication, Censys observes approximately 47 hosts matching this signature globally, though we note that this number fluctuates based on migration patterns.
Infrastructure Analysis
Mapping the compromised hosts reveals an infrastructure topology that closely mirrors known avian migration routes along the Atlantic Flyway. The threat actor’s primary staging area appears to be located in a public park in Washington, DC, based on carrier GPS telemetry data recovered from intercepted microSD cards.
Key infrastructure observations:
- C2 servers are concentrated along the US Eastern Seaboard, with outliers in London and, inexplicably, one compromised host on a research vessel in the North Atlantic
- Carrier routes follow established flyways, making geographic attribution unreliable
- Operational tempo decreases significantly during winter months, which we initially attributed to operational security practices but now believe is simply because the pigeons migrate south
- Bandwidth peaks during spring mating season, when carrier availability is highest
Attempts to traceroute the infrastructure have been unsuccessful. The carriers keep returning to the wrong coop.
Indicators of Compromise
Organizations should monitor for the following indicators:
Network-Based IOCs
| Indicator | Type | Description |
HTTP 418 I'm a Teapot | HTTP Response | All responses from compromised hosts |
BREW | HTTP Method | Non-standard method from HTCPCP |
application/coffee-pot-command | Content-Type | HTCPCP payload content type |
X-Spout: ready | HTTP Header | BrewJack-specific header |
Port 80 serving HTCPCP | Service | Protocol confusion indicator |
Host-Based IOCs
| Indicator | Description |
| Feathers near server racks | Physical evidence of carrier ingress |
| Seed packets in the mail room | Supply chain indicator (carrier feed) |
| Cooing sounds from the DMZ at 3 AM | Carrier homing signal cron job |
| Unexplained frequent flyer miles on the corporate travel account | IPoAC QoS side effect |
| Droppings on rooftop ventilation units | Carrier staging area residue |
/etc/cron.d/pigeon_call | Persistence mechanism |
File Hashes (SHA-256)
c00c00c00c00c00c00c00c00c00c00c00c00c00c00c00c00c00c00c00c00c00c brewjack_agent.py
4e5t4e5t4e5t4e5t4e5t4e5t4e5t4e5t4e5t4e5t4e5t4e5t4e5t4e5t4e5t4e5t pigeon_call.sh
b1rdb1rdb1rdb1rdb1rdb1rdb1rdb1rdb1rdb1rdb1rdb1rdb1rdb1rdb1rdb1rd htcpcp_server.bin
TTPs (MITRE ATT&CK Mapping)
We have mapped Pigeon Forge’s techniques to the MITRE ATT&CK framework, though several required the creation of new sub-techniques:
| Tactic | Technique | Description |
| Initial Access | T1190.pigeon: Exploit Public-Facing Birdfeeder | Compromise via poisoned seed at target facility |
| Execution | T1059.avian: Avian Scripting | Commands delivered via carrier-borne microSD |
| Persistence | T1053.coo: Scheduled Cooing | Cron-based carrier homing signal |
| Defense Evasion | T1036.418: Masquerading as Teapot | All responses return 418 to avoid alerting |
| C2 | T1071.2549: IPoAC Communication | Command and control over avian carriers |
| Exfiltration | T1048.bird: Exfiltration Over Avian Protocol | Data exfiltration via outbound carriers |
| Collection | T1560.nest: Archive via Nesting | Data staged in physical nesting sites |
Attribution
Pigeon Forge probably operates out of a park bench in Washington, DC. Attribution is based on:
- GPS telemetry recovered from intercepted carriers consistently originates from a 50-meter radius in Dupont Circle
- Breadcrumb purchase records from a nearby bakery correlate with increased carrier activity
- The group’s operational security is otherwise strong: carriers are self-keying when using public key encryption (per RFC 2549), and the group avoids NATs because, as the RFC notes, the carriers may eat them
The threat actor’s motivation remains unclear. No ransom demands have been made. No data has been confirmed exfiltrated. The compromised servers are merely teapots now. We cannot rule out that this is performance art.
Affected Vendors
We attempted responsible disclosure to the following vendors:
| Vendor | Response |
| RFC 2549 Carrier Consortium | “Working as intended” |
| IETF HTCPCP Working Group | “This is not our problem. Try the Teapot Advisory Board.” |
| US Fish & Wildlife Service | “Please stop calling us about cybersecurity” |
| Ashburn Datacenter Facilities | “We already have a cat” |
Mitigations
Censys recommends the following mitigations:
- Install bird netting on all rooftop access points, ventilation units, and satellite dishes
- Implement strict source routing (RFC 2549 warns this is a choke-point)
- Deploy scarecrows in the DMZ (ensure they do not interfere with existing physical security)
- Block HTTP 418 at the WAF if your servers are not, in fact, teapots
- Monitor for the BREW HTTP method in web server logs
- Remove all birdfeeders within 100 meters of datacenter facilities
- Do not leave breadcrumbs near the server room
- Audit your frequent flyer accounts for unexplained mileage accrual
- Consider upgrading carrier QoS from Business to Concorde class. If you can’t beat them, at least get the bonus miles
Conclusion
BrewJack mixes physical and digital attack vectors in a way that sidesteps typical network monitoring. The campaign’s impact has been limited: the main damage is that 47 servers now insist they are teapots. Using RFC 2549 for C2 adds a transport layer that traditional IDS/IPS tools do not see.
The average TTL of an avian carrier is 15 years, so defenders should plan for a long-term persistence threat. We will continue to monitor migration patterns and update this advisory as the situation evolves.
Censys customers can use the search query provided above to identify affected assets in their attack surface. We have also added the pigeon-forge tag to all known compromised hosts in the Censys platform.
For questions about this advisory, please contact research@censys.com. Do not attempt to contact us via carrier pigeon.
Censys does not endorse, condone, or recommend the use of avian carriers for network communication. All pigeons referenced in this advisory have been safely relocated to a farm upstate. No teapots were harmed in the production of this report.
Published 1 April 2026. Happy April Fools’ Day from Censys ARC.