Putting Exploits into Context
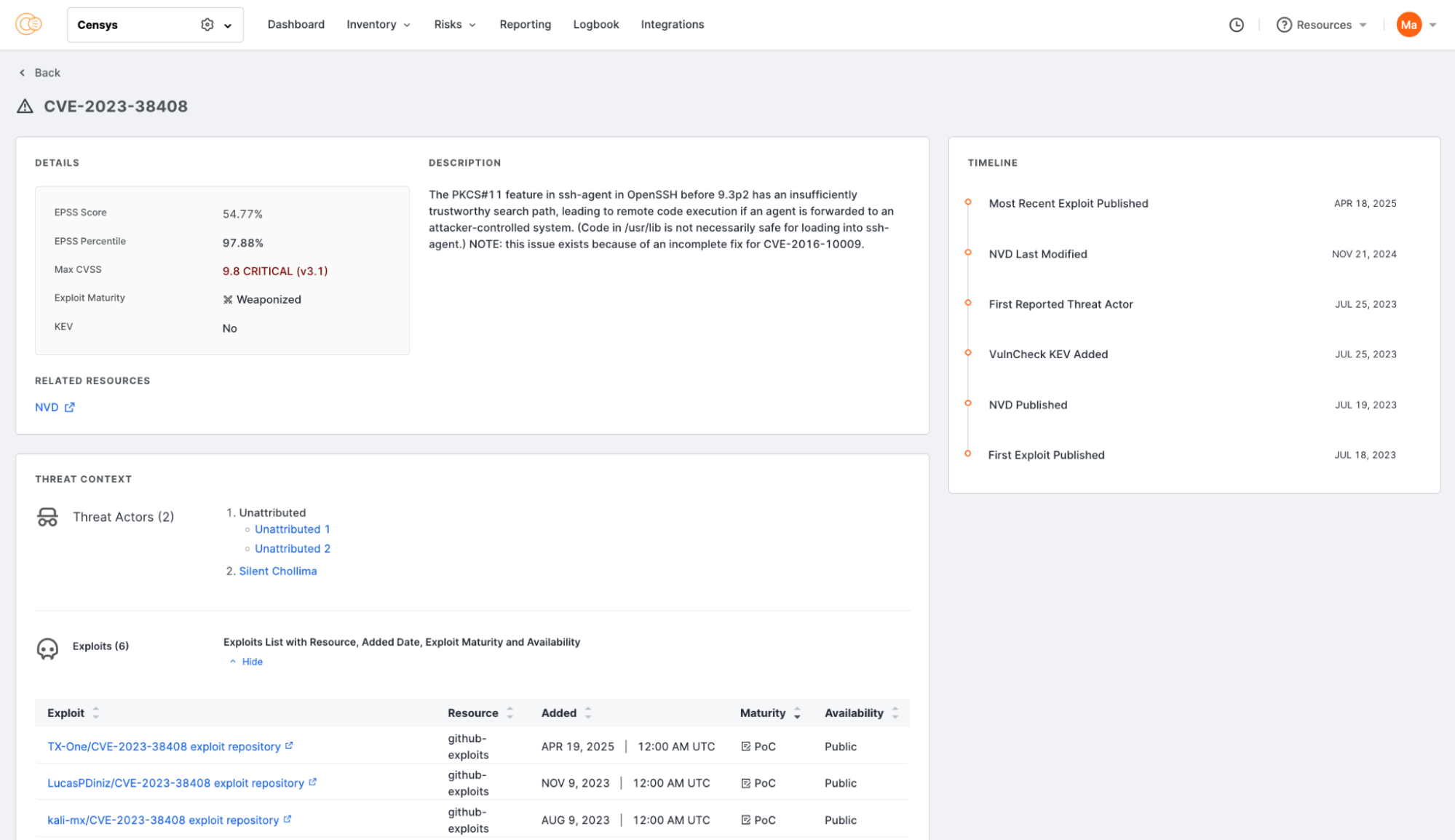
Understanding which vulnerabilities matter most can be a daunting task. The new CVE Exploit Context feature in Censys ASM changes that by offering clear, actionable insight into which CVEs are truly dangerous and exploited by attackers in the wild.
What Is CVE Exploit Context?
CVE Exploit Context delivers threat intelligence context on whether a vulnerability:
- Has been exploited in the wild
- Is being used by specific threat actors, ransomware groups, or botnets
- Has a documented POC exploit
Each entry is backed by links to more detailed data, helping analysts trace the threat landscape around each CVE, as well as allowing red teams to simulate attacks for documented exploits.
Why This Matters: Smarter Prioritization
Not all vulnerabilities are created equal. In fact, research from VulnCheck reveals:
- Only 1.1% of vulnerabilities are ever actively exploited.
- If a CVE has a known exploit proof-of-concept (POC), there’s a 72.9% chance it will be exploited in real attacks.
With this context baked into ASM, security teams can instantly pinpoint which vulnerabilities deserve urgent attention—cutting through the noise and saving valuable time and resources.
The Bottom Line: Actionable Security Starts with Context
The CVE Exploit Context release is another critical capability that helps improve vulnerability management. By surfacing exploit evidence and attacker activity, it empowers teams to make smarter, faster decisions. For organizations looking to stay ahead of evolving threats, this kind of visibility isn’t just helpful, it’s essential.
To learn more about the new CVE Exploit Context and Censys’s Attack Surface Management solution, sign up for a demo walk through today.