Vulnerability Description
CVE-2026-3055 is a critical out-of-bounds read vulnerability in NetScaler ADC and NetScaler Gateway resulting from insufficient input validation. The flaw was assigned a critical CVSS v4.0 base score of 9.3. Exploitation requires no authentication, no user interaction, and no special preconditions beyond the appliance being configured as a SAML Identity Provider (IDP). Successful exploitation could allow an unauthenticated remote attacker to read sensitive memory contents.
Administrators can verify if SAML is enabled by checking NetScaler configuration for:
add authentication samlIdPProfile .*
A second vulnerability, CVE-2026-4368 (CVSS 4.0: 7.7 High), was disclosed in the same bulletin. It involves a race condition causing user session mixup when configured as a Gateway or AAA virtual server. Exploitation requires low-privilege authentication and adjacent timing conditions. Only version 14.1-66.54 is affected for this second vulnerability.
| Field | Description |
| CVE-ID | CVE-2026-3055 — CVSS v4.0 9.3— assigned by NetScaler |
| Vulnerability Description | CVE-2026-3055 is a critical out-of-bounds read vulnerability in NetScaler ADC and NetScaler Gateway resulting from insufficient input validation. Exploitation requires no authentication, no user interaction, and no special preconditions beyond the appliance being configured as a SAML Identity Provider (IDP). Successful exploitation could allow an unauthenticated remote attacker to read sensitive memory contents. |
| Date of Disclosure | March 23, 2026 |
| Affected Assets | NetScaler ADC and NetScaler Gateway |
| Vulnerable Software Versions | NetScaler ADC/Gateway 14.1 before 14.1-66.59 NetScaler ADC/Gateway 13.1 before 13.1-62.23 NetScaler ADC 13.1-FIPS/NDcPP before 13.1-37.262 NetScaler ADC 12.1 and 13.0 are EOL and will not receive patches |
| PoC Available | No public PoC or exploit code is available. The vulnerability was discovered by Cloud Software Group. |
| Exploitation Status | No active exploitation observed at time of disclosure (March 23, 2026). |
| Patch Status | Patches are currently available for supported versions. Given the critical nature of these vulnerabilities and the lack of authentication required for exploitation, we strongly urge admins to apply the relevant updates immediately. NetScaler ADC and Gateway 14.1-66.59 or later NetScaler ADC and Gateway 13.1-62.23 or later NetScaler ADC 13.1-FIPS/NDcPP 13.1-37.262 or later |
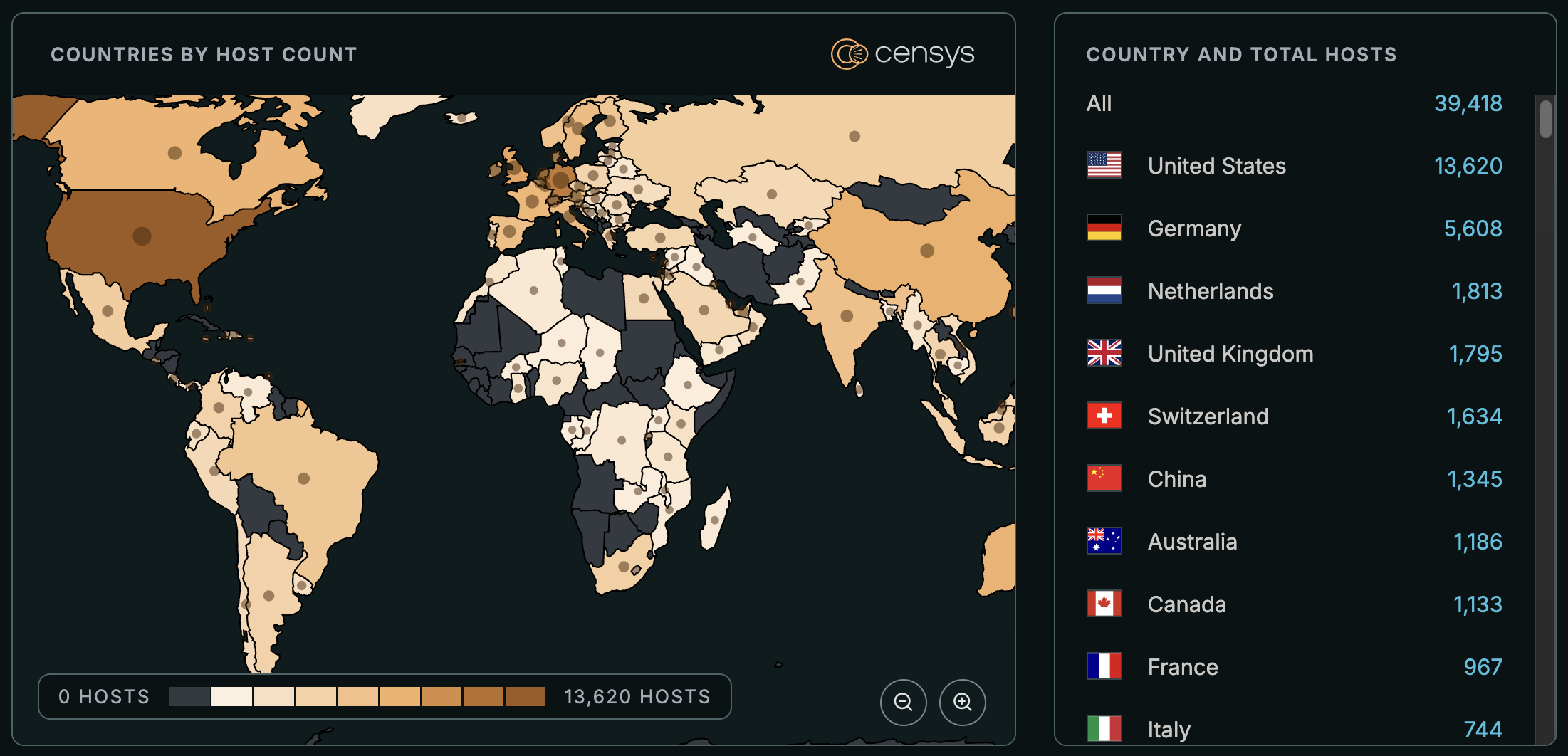
Censys ARC Perspective
At the time of writing, Censys observes 173K exposed Web Properties.
Note that a single IP address often supports many distinct applications by hosting them on different ports or distinguishing them by hostname (Virtual Hosting). Consequently, scanning for ‘Web Properties’ identifies every unique service running on the server, whereas scanning by IP alone consolidates them into a single record. This is why the number of Web Properties observed often differs from the IP-based location map shown above.
Exposed Hosts and Web Properties are trackable with the following queries:
(host.services.software: (vendor="citrix" and product={"netscaler gateway", "netscaler"}) or web.software: (vendor="citrix" and product={"netscaler gateway", "netscaler"})) and not labels="HONEYPOT"
host.services.software: (vendor="Citrix" and product={"NetScaler Gateway", "NetScaler"}) or web_entity.instances.software: (vendor="Citrix" and product={"NetScaler Gateway", "NetScaler"})services.software: (vendor="Citrix" and product={"NetScaler Gateway", "NetScaler"}) and not labels: {honeypot, tarpit}





