Vulnerability Description
A critical authentication bypass vulnerability (CVSS v3.1 base score 9.3) in SmarterTools’ SmarterMail software that allows unauthenticated attackers to reset administrator accounts without verifying credentials or reset tokens. The vulnerability affects SmarterMail Build 9510 and earlier versions and is being actively exploited in the wild. It is important to note that the patch for the earlier arbitrary file upload vulnerability just a few weeks prior, CVE-2025-52691, does not address this newer vulnerability.
This newer vulnerability enables attackers to reset administrator accounts through the /force-reset-password API endpoint without authentication. Since SmarterMail administrator privileges include the ability to execute operating system commands, successful exploitation results in complete administrative compromise with system level access on the underlying host. Attackers could potentially abuse compromised servers to establish persistence, execute commands, steal data, or launch further attacks within your network. Proof-of-concept exploits are publicly available on GitHub and have been detailed in technical blogs, making this a high-priority remediation target.
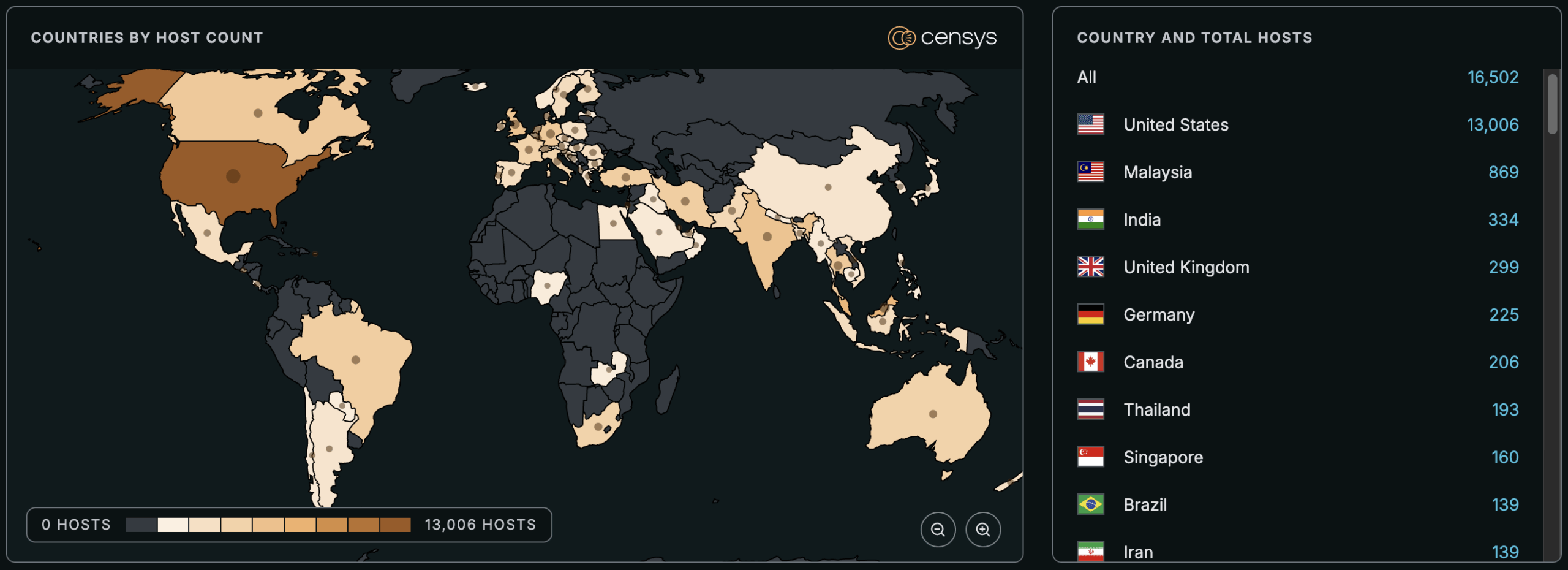
See the full breakdown by country in Censys Platform →
| Field | Description |
| CVE-ID | CVE-2026-23760 — CVSS v3.1 base score 9.3 — assigned by VulnCheck |
| Vulnerability Description | A critical vulnerability in SmarterTools’ SmarterMail software allows unauthenticated attackers to reset administrator accounts without verifying credentials or reset tokens. Successful exploitation results in complete administrative compromise with system level access on the underlying host. |
| Date of Disclosure | January 22, 2026 |
| Affected Assets | SmarterTools SmarterMail |
| Vulnerable Software Versions | Build 9510 and all prior builds. |
| PoC Available | Yes. Proof-of-concept exploits are publicly available on GitHub and have been detailed in technical blogs (e.g., WatchTowr, Huntress). The exploit is low-complexity, requiring only a single HTTP POST request to the vulnerable API endpoint. |
| Exploitation Status | This vulnerability is being actively exploited in the wild, making it a high-priority remediation target. Users have reported new accounts unexpectedly appearing on their servers on the SmarterTools forum, which appears related. Additionally, CISA added CVE-2025-52691 to their Known Exploited Vulnerabilities on January 26, 2026. |
| Patch Status | This has been fixed in build 9511 (and later), and is available through the SmarterTools downloads page.Note: The patch for the earlier arbitrary file upload vulnerability just a few weeks prior, CVE-2025-52691, does not address this newer vulnerability. |
Censys Perspective
At the time of writing, Censys observes 157,429 exposed Web Properties.
Note that a single IP address often supports many distinct applications by hosting them on different ports or distinguishing them by hostname (Virtual Hosting). Consequently, scanning for ‘Web Properties’ identifies every unique service running on the server, whereas scanning by IP alone consolidates them into a single record. This is why the number of Web Properties observed often differs from the IP-based location map shown above.
Exposed host and Web Properties are trackable with the following queries:
(host.services.endpoints.http.body: {"ng-app="smartermail"", "SmarterMail Copyright"} or host.services.endpoints.http.html_title="rntSmarterMailrn" or host.services.endpoints.http.favicons.hash_md5="1af343c2b059ae3da7b4a144d05db588")
or
(web.endpoints.http.body: {"ng-app="smartermail"", "SmarterMail Copyright"} or web.endpoints.http.html_title="rntSmarterMailrn" or web.endpoints.http.favicons.hash_md5="1af343c2b059ae3da7b4a144d05db588")risks.name="Vulnerable SmarterMail [CVE-2026-23760]"services.http.response.body: {"SmarterMail Copyright","ng-app="smartermail""} or services.http.response.html_title="rntSmarterMailrn" or services.http.response.favicons.md5_hash="1af343c2b059ae3da7b4a144d05db588"





