Vulnerability Description
CVE-2026-32746 is a critical pre-authentication remote code execution (RCE) vulnerability in the telnet daemon (telnetd) shipped with GNU Inetutils through version 2.7. The flaw is a stack-based buffer overflow in the LINEMODE SLC (Set Local Characters) suboption handler (telnetd/slc.c). An unauthenticated attacker with network access to a telnet port can exploit this during option negotiation, before authentication occurs.
The add_slc() function writes three bytes per SLC triplet into a fixed 108-byte buffer (slcbuf) without checking whether space remains. After 35 triplets with function codes greater than 18, the write exceeds the buffer boundary and corrupts adjacent memory, including a pointer later used for an arbitrary write. Because telnetd often runs as root under inetd or xinetd, successful exploitation could potentially grant an attacker control of the host, particularly on embedded systems or other environments where modern protections like ASLR or PIE are not enabled or available.
| Field | Description |
| CVE-ID | CVE-2026-32746 — CVSS 9.8 — assigned by MITRE |
| Vulnerability Description | CVE-2026-32746 is a critical pre-authentication RCE vulnerability in the telnet daemon (telnetd) shipped with GNU Inetutils. The flaw is a stack-based buffer overflow in the LINEMODE SLC (Set Local Characters) suboption handler (telnetd/slc.c). An unauthenticated attacker with network access to a telnet port can exploit this during option negotiation, before authentication occurs. |
| Date of Disclosure | March 13, 2026 |
| Affected Assets | The telnet daemon (telnetd) shipped with GNU Inetutils. GNU Inetutils telnetd is packaged in most major Linux distribution repositories and may be running on servers, embedded devices, or network appliances. |
| Vulnerable Software Versions | All versions through 2.7, which is the current upstream release. |
| PoC Available | Yes. The original disclosure by the DREAM Security Research Team on the bug-inetutils mailing list includes a technical writeup. A public exploit repository is also available on GitHub. The Censys ARC research team has independently verified that this exploit reliably crashes a default Inetutils telnetd installation. |
| Exploitation Status | No confirmed in-the-wild exploitation has been reported as of this writing. The EPSS score remains low (0.04%). However, the availability of a public exploit, the zero-interaction attack surface, and the root-level impact make active exploitation plausible, particularly against embedded devices or systems where protections are not available. |
| Patch Status | No new upstream GNU Inetutils release has been issued. A fix commit exists in the Inetutils git repository. Debian has applied the fix in unstable/sid (2:2.7-4), but Debian stable releases (bullseye, bookworm, trixie) remain vulnerable as of March 18, 2026. |
Censys ARC Perspective
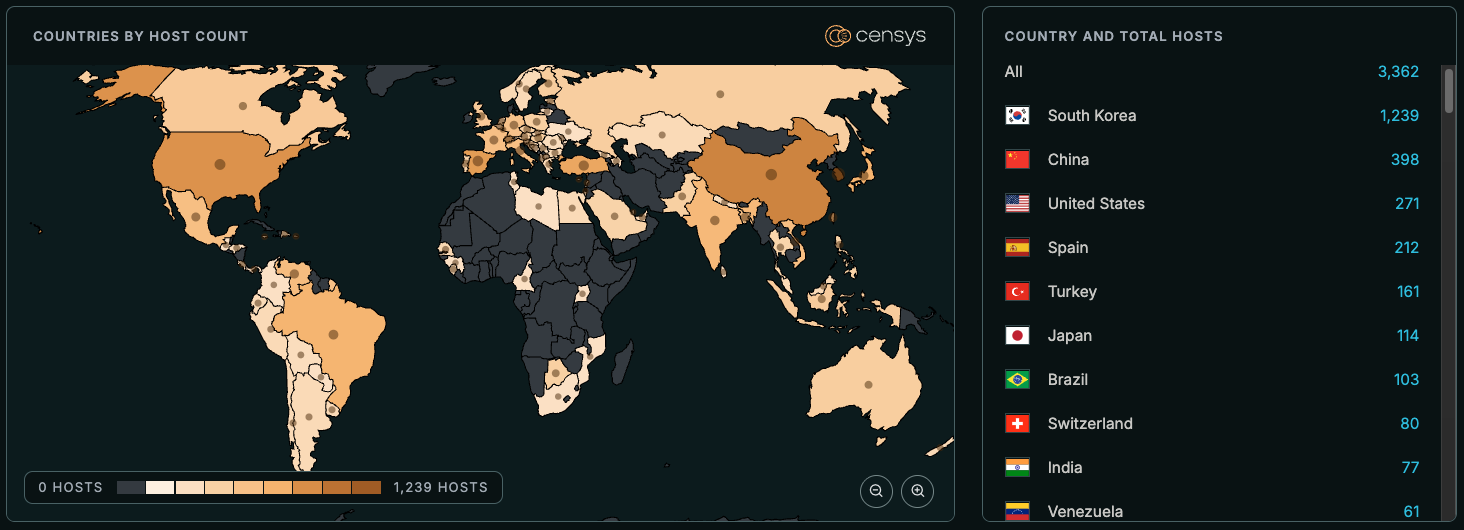
At time of writing, Censys sees 3,362 exposed hosts, trackable with the following queries:
host.services: (protocol: "TELNET" and banner=~"\\w+\\s+[0-9]+\\.[0-9]+(\\.[0-9]+)*(-[\\w-]+)?\\s+\\([^)]+\\)\\s+\\([^)]+\\)")host.services.telnet.banner: /.w+s+[0-9]+.[0-9]+./
services: (service_name="TELNET" and banner:/.*\w+ [0-9]+\.[0-9]+.* [(].*[)] [(].*[)].*/)






